The Health Insurance Portability and Accountability Act (HIPAA) is a federal law that sets national standards for the privacy, security, and electronic exchange of personal health information in the United States.
If your organization handles any form of health data in the U.S., it's imperative that you comply with HIPAA regulations. Failing to do so could result in reputational damages, significant fines, and even criminal prosecution.
In this article, we'll break down what HIPAA entails, to whom it applies, what it requires, actionable steps and insights for compliance, penalties for non-compliance, and more. Let's get started.
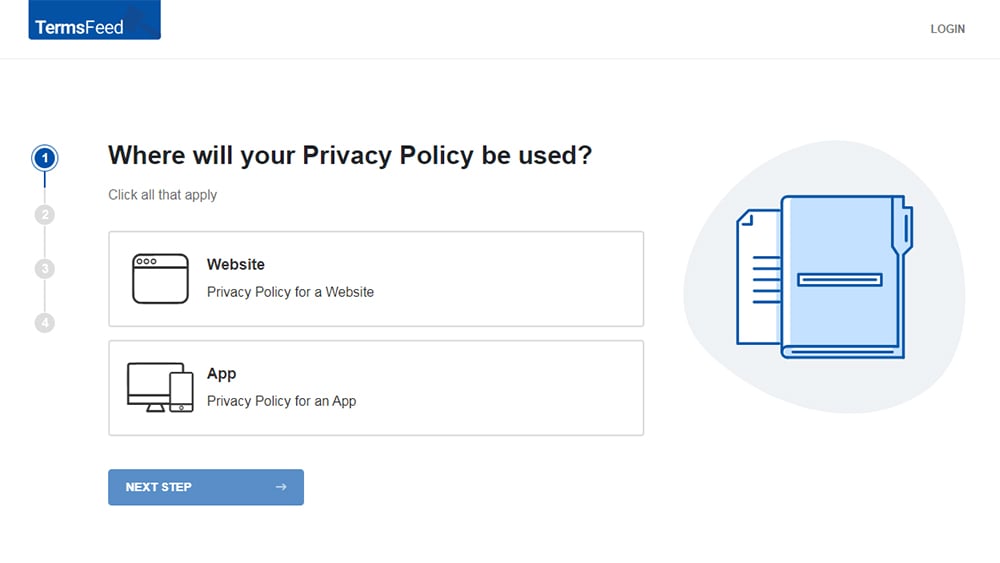
Our Privacy Policy Generator makes it easy to create a Privacy Policy for your business. Just follow these steps:
-
At Step 1, select the Website option or App option or both.
-
Answer some questions about your website or app.
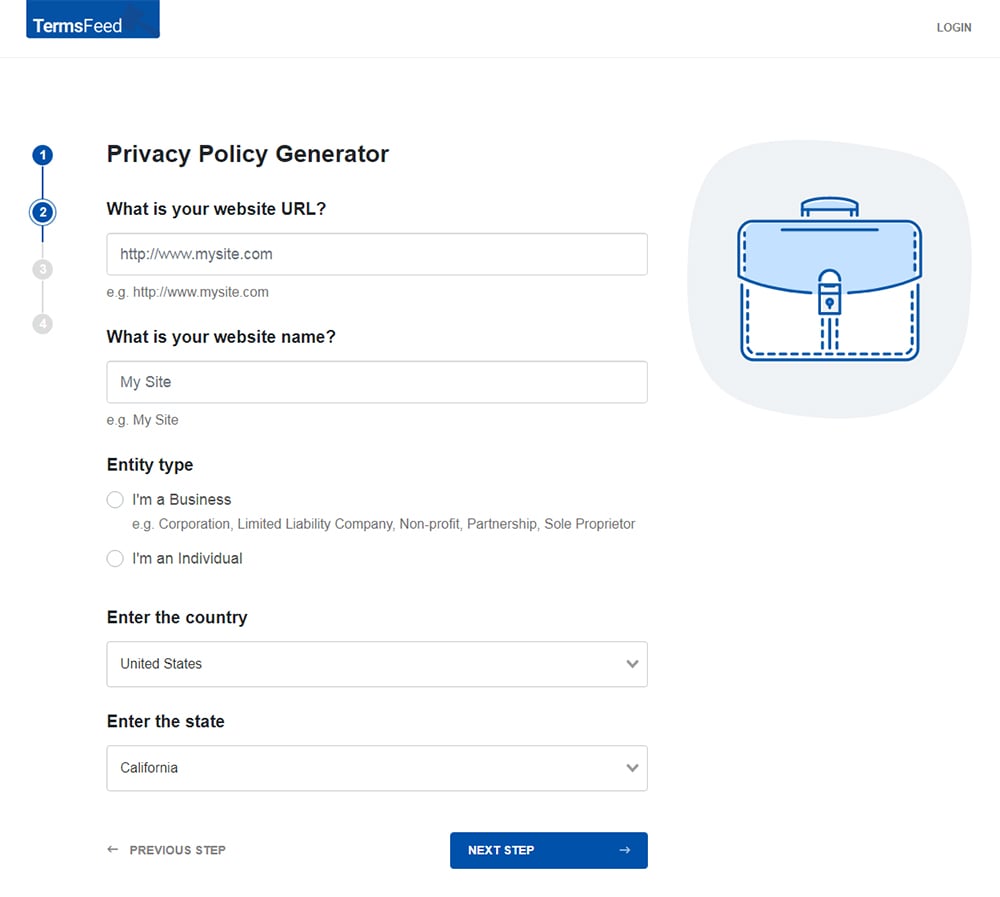
-
Answer some questions about your business.
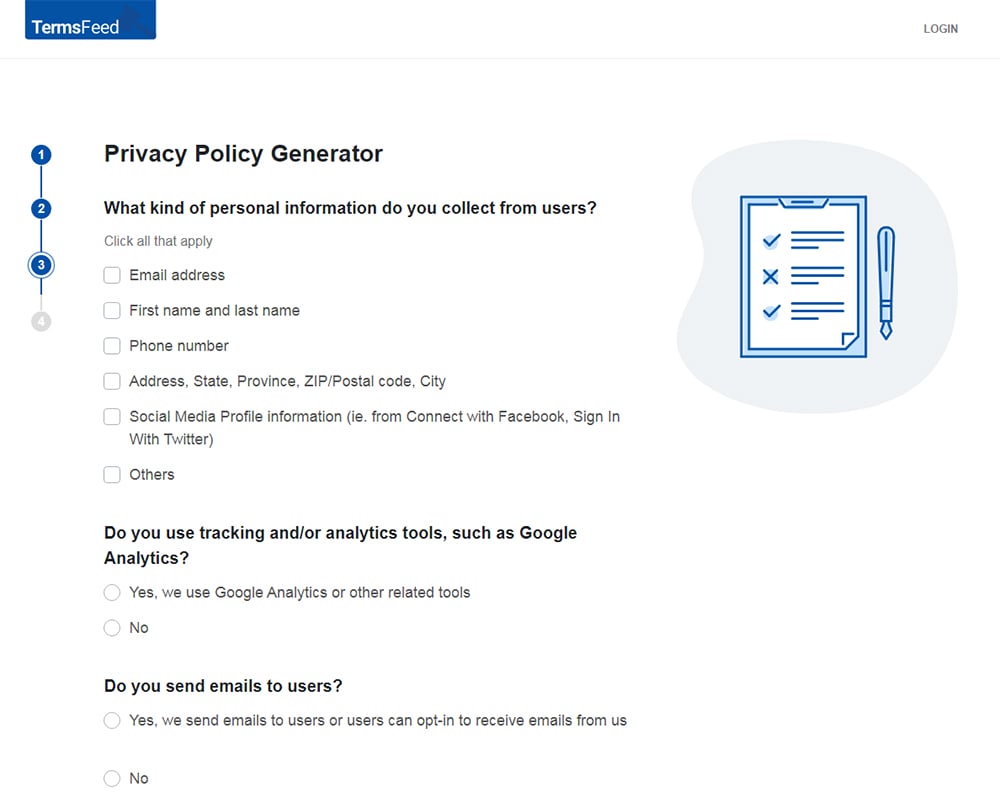
-
Enter the email address where you'd like the Privacy Policy delivered and click "Generate."
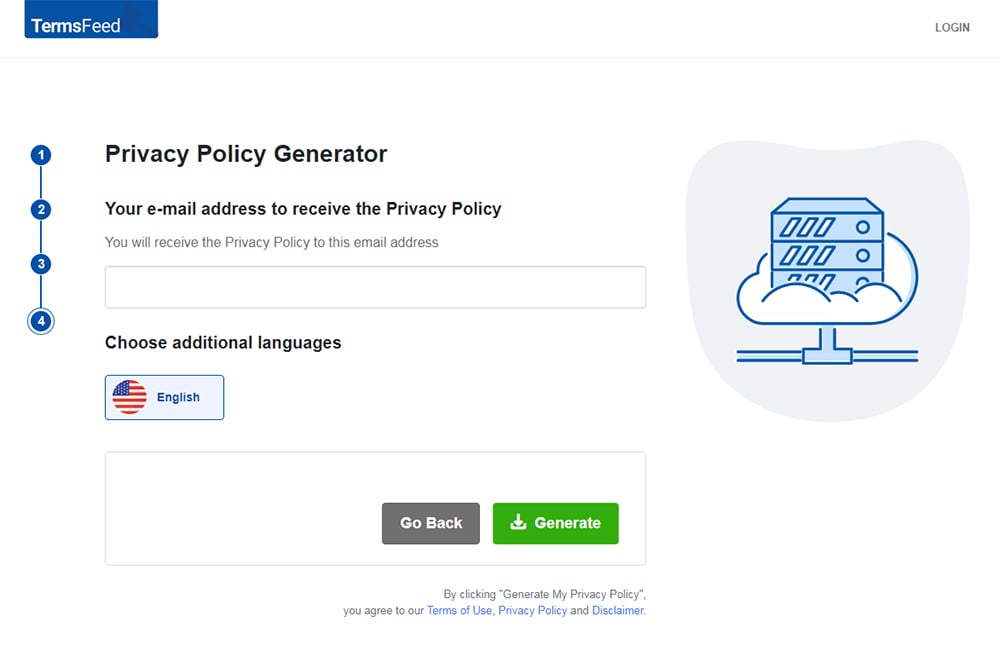
You'll be able to instantly access and download your new Privacy Policy.
- 1. What is the Health Insurance Portability and Accountability Act (HIPAA)?
- 1.1. What is Protected Health Information (PHI)?
- 2. Titles and Rules of the Health Insurance Portability and Accountability Act (HIPAA)
- 3. Who Does HIPAA Apply to?
- 3.1. Covered Entities
- 3.2. Business Associates
- 4. Requirements and Best Practices for Compliance with HIPAA
- 4.1. Implement Sufficient Security Safeguards
- 4.2. Observe Individual Rights Under HIPAA
- 4.3. Conduct Regular Risk Assessments
- 4.4. Notify of Data Breaches
- 4.5. Provide a Notice of Privacy Practices
- 4.6. Maintain Business Associate Agreements (BAAs)
- 4.7. Minimize Disclosure of PHI
- 5. The Health Insurance Portability and Accountability Act (HIPAA) and Your Privacy Policy
- 5.1. Introductory Clause
- 5.2. Uses and Disclosures of PHI
- 5.3. Individual Privacy Rights
- 5.4. Contact Information for Questions and Complaints
- 6. Penalties for Non-Compliance with HIPAA
- 7. Summary
- 8. All US Privacy Laws
What is the Health Insurance Portability and Accountability Act (HIPAA)?
The Health Insurance Portability and Accountability Act (HIPAA) is a federal legislation enacted by the 104th U.S. Congress and signed into law by President Bill Clinton on August 21, 1996.
HIPAA was originally designed to provide ongoing health insurance coverage for U.S. workers between jobs, hence the "insurance portability" component in its name.
However, after several modifications over the years, HIPAA is now best known for its rules that govern the collection, use, and disclosure of patients' personal health information.
In short, HIPAA does the following:
- Prohibits applicable businesses from disclosing personal health information without a patient's authorization
- Minimizes the risk of healthcare fraud and abuse
- Makes it easier for workers to maintain health insurance coverage when they lose or change jobs
- Sets national standards for safeguarding the privacy and security of Protected Health Information or "PHI."
What is Protected Health Information (PHI)?
Protected Health Information (PHI) is also known as "individually identifiable health information." It's essentially any information that can be used to identify a person and was created, used, or disclosed while providing a healthcare service.
PHI can be in any form, including electronic, paper, or oral communication. Under HIPAA, examples of PHI include:
- Demographic information, such as names, addresses, phone numbers, ID numbers, etc.
- Medical information, such as diagnoses, lab test results, treatment plans, prescriptions, etc.
- Insurance information, such as claims, policy numbers, and billing information
- Health-related information, such as mental health records, substance abuse treatment records, genetic information, etc.
- Any other information that can identify an individual and relates to their health
It's important to note that PHI doesn't include "de-identified" health information. De-identified information is any data that has been stripped of all direct identifiers (e.g., names, ID numbers, etc.) that could identify an individual.
PHI can be interpreted broadly. Therefore, when in doubt, err on the side of caution and consider all health-related information as PHI.
Titles and Rules of the Health Insurance Portability and Accountability Act (HIPAA)

HIPAA's provisions are considerably broad in scope, featuring several titles and rules that regulate the privacy and security of U.S. health information.
HIPAA titles are distinct components of the law that address different aspects of healthcare information management. They are as follows:
- Title I: Health Insurance Reform
- Title II: Administrative Simplification
- Title III: Tax-Related Health Provisions
- Title IV: Application and Enforcement of Group Health Insurance Requirements
- Title V: Revenue Offsets
Among these, Title II is most relevant for applicable businesses. In fact, HIPAA compliance in the healthcare space typically means observing the provisions of this title.
Title II outlines several guidelines (collectively known as the "HIPAA rules") for safeguarding Protected Health Information (PHI).
For our purposes, the HIPAA Privacy Rule, Security Rule, Breach Notification Rule, and Enforcement Rule are the most important to consider.
Let's briefly examine each.
-
HIPAA Privacy Rule: This rule specifies how PHI can be lawfully collected, used, and shared, as well as the rights individuals have over their PHI.
The Privacy Rule requires organizations to implement policies and procedures to ensure the privacy, security, and confidentiality of PHI at all times. It also requires organizations to obtain written consent from individuals before using or disclosing their PHI.
-
HIPAA Security Rule: An extension of the Privacy Rule, HIPAA's Security Rule requires organizations to implement administrative, technical, and physical safeguards to protect electronic PHI (ePHI) from unauthorized access, use, and disclosure.
-
HIPAA Breach Notification Rule: Under this rule, organizations must promptly notify affected individuals, the Department of Health and Human Services (HHS), and, in some cases, the media if a breach of unsecured PHI occurs.
-
HIPAA Enforcement Rule: The Enforcement Rule provides guidance on HIPAA violations and the penalties for non-compliance. It clarifies how the HHS Office for Civil Rights (OCR) will investigate and enforce these penalties.
Now that we understand what HIPAA entails and the type of data it protects, let's take a look at which organizations must comply with its rules.
Who Does HIPAA Apply to?
HIPAA applies to two main business categories: "Covered Entities" and "Business Associates." If your organization falls under either of these categories, you must comply with HIPAA's rules identified above.
Let's take a closer look.
Covered Entities
Covered entities are HIPAA's primary targets since they directly handle PHI in the United States. They can be classified into three distinct groups:
-
Healthcare Providers, including but not limited to:
- Hospitals
- Doctors
- Dentists
- Psychologists
- Chiropractors
- Nursing homes
- Pharmacies
-
Health Plans, including but not limited to:
- Health insurance companies
- HMOs
- Medicare
- Medicaid
- Employer-sponsored health plans
-
Healthcare Clearinghouses: These are entities that convert nonstandard health information into standard formats and vice versa, such as:
- Billing services
- Community health management information systems
- Repricing companies
Business Associates
Business associates are individuals or organizations that provide services involving the use or disclosure of PHI to covered entities.
Examples of business associates include:
- Medical billing companies
- Healthcare claims processing companies
- Lawyers
- Accountants
- Email hosting providers
- Records storage companies
- Records destruction companies
- Medical transcription services
It's important to note that HIPAA also applies to subcontractors. These are entities that provide PHI-driven services to business associates. In other words, they are business associates of existing business associates.
Subcontractors typically provide IT support, cloud storage, data backup, and similar services to business associates.
Requirements and Best Practices for Compliance with HIPAA

In light of the HIPAA rules, covered entities and their business associates must perform several key obligations to ensure the privacy and security of PHI.
Below, we outline these obligations and provide practical steps for your organization to comply accordingly.
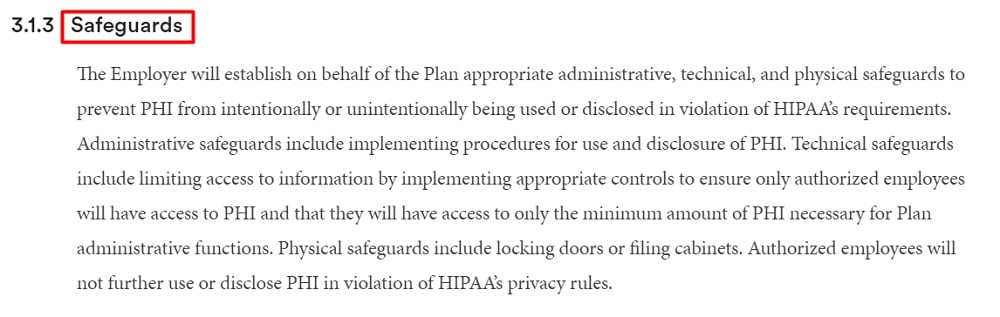
Implement Sufficient Security Safeguards
Under HIPAA's Security Rule, covered entities and their business associates must have safeguards in place to ensure the privacy, confidentiality, and integrity of PHI, specifically in its electronic form (i.e., ePHI).
The Security Rule expands on this provision by setting out three types of safeguards you must implement as a covered entity or business associate. They include administrative, physical, and technical safeguards.
-
Administrative safeguards, such as:
- Designating a qualified privacy officer to oversee HIPAA compliance
- Training employees on HIPAA compliance
- Managing security processes and procedures
- Limiting PHI access to only authorized personnel
- Developing strategies and policies to deal with security incidents and breaches
-
Physical Safeguards, such as:
- Restricting access to PHI storage facilities, e.g., through secure locks and CCTV surveillance
- Implementing policies to ensure that workstations and devices are protected (for example, locking computer screens when not in use)
- Developing a process for properly disposing of electronic media containing PHI
-
Technical Safeguards, such as:
- Setting up effective cybersecurity systems and processes, e.g., private networks, digital signatures, firewalls, etc.
- Encrypting PHI
- Employing multi-factor authentication
For example, here's how Brown University concisely explains its safeguards for protecting PHI in its HIPAA Privacy Policy:
Observe Individual Rights Under HIPAA
Under the HIPAA Privacy Rule, individuals have the right to:
- Obtain a copy of their medical records and other health information
- Request corrections to inaccuracies in their health information
- Ask covered entities to limit the use or disclosure of their health information for specific purposes
- Understand how covered entities and business associates will use and disclose their health information
- Withdraw their permissions to use or disclose their health information
- File a complaint with the HHS if they believe their HIPAA rights have been violated
While these rights may not apply in all situations, it's important that you observe and help patients exercise them where practical.
Conduct Regular Risk Assessments
Under HIPAA's Security Rule, you must conduct regular risk assessment programs and record the results. This helps you identify and mitigate potential threats and vulnerabilities to PHI (both physical and electronic) before they become actual security incidents.
For instance, if your risk assessment determines that your organization's network is not secure, you can implement additional data security measures like firewalls and encryption to prevent potential breaches.
Notify of Data Breaches
Under its Breach Notification Rule, HIPAA specifies what steps covered entities and their business associates must take if a breach of unsecured PHI occurs. Note that this requirement doesn't apply to secured PHI, such as encrypted data.
HIPAA classifies data breaches into two categories based on the number of individuals affected and the level of risk to the PHI involved.
-
If the breach affects 500 or fewer people, it's considered a "minor breach." In this case, you must notify the affected individuals within 60 days of discovering the breach.
Furthermore, you must keep a record of the breach and report it to the Department of Health and Human Services (HHS) by the 60th day of the following calendar year. For instance, if a breach is discovered on December 1st, 2022, you must report it to the HHS by February 28th, 2023.
-
If the breach affects more than 500 people, it's considered a "major breach." In this case, you must notify the affected individuals and the HHS within 60 days of discovering the breach.
You must also inform a prominent media outlet and the local law enforcement agency in the jurisdiction where the breach occurred.
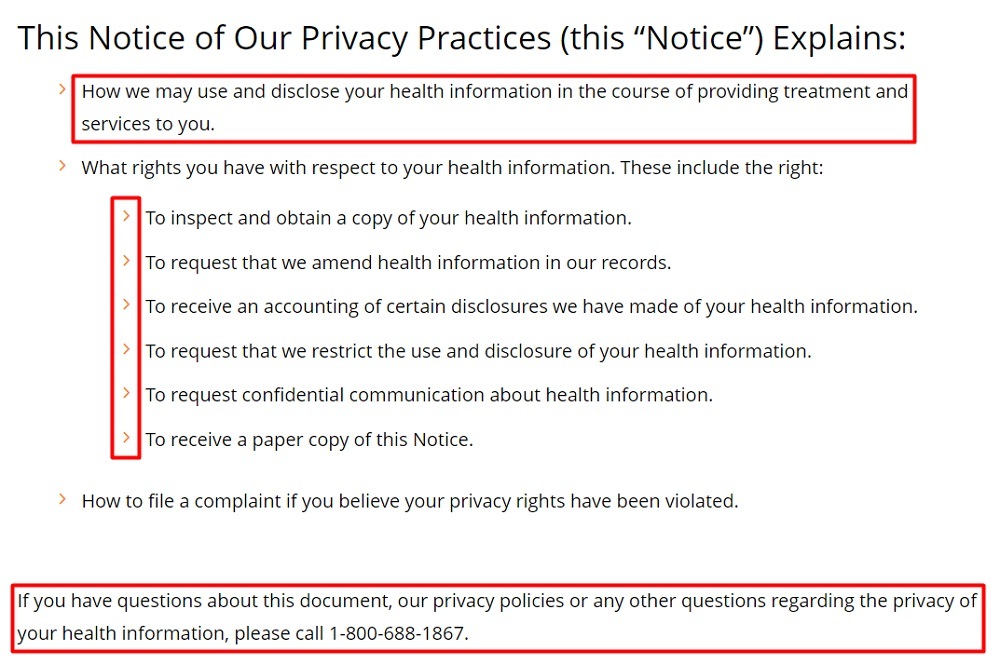
Provide a Notice of Privacy Practices
Providing a Notice of Privacy Practices (NPP) is a crucial obligation imposed on covered entities and business associates under the HIPAA Privacy Rule.
This notice must include the following details:
- A description of how the Privacy Rule allows your organization to use and disclose PHI, as well as the need for the patient's consent before you can disclose their PHI
- Your obligations to ensure the privacy and security of PHI
- Individual HIPAA privacy rights, including the right to complain to you or the HHS if they believe their rights have been violated
- Your organization's contact details to allow patients to get more information or submit a complaint
Additionally, you must present your NPP to patients several times and in different ways. The highlights are as follows:
- Provide your NPP at the first appointment with a patient, including after an emergency or when the patient enrolls in a healthcare plan.
- Send a reminder at least once every three years to inform patients that they can request your NPP whenever they wish.
- Conspicuously display your NPP so patients don't miss it.
- Display your NPP on your organization's website if you have one. It could be included in your HIPAA Privacy Policy or hosted separately.
Finally, HIPAA sets out the following rules for patients acknowledging receipt of your NPP:
- You must ask patients to sign a written statement acknowledging receipt of your NPP.
- If the patient does sign, you don't have the right to use or disclose the patient's data for a different purpose.
- If the patient refuses to sign, you must keep a record of the refusal. However, you can still use or disclose the patient's data in line with HIPAA's provisions.
Here's how Duke Health displays the highlights of its Notice of Privacy Practices before addressing the exact details later on:
Maintain Business Associate Agreements (BAAs)
Under HIPAA, a covered entity must draft and enforce a Business Associate Agreement (BAA) for every partnership involving the use or disclosure of PHI.
These agreements define the business associate's responsibilities under HIPAA, including guidelines for protecting PHI and reporting any security incidents or breaches.
Ultimately, BAAs help ensure that PHI is protected throughout the entire chain of entities that handle it, from covered entities to business associates to subcontractors.
Minimize Disclosure of PHI
As a covered entity or business associate, you must ensure that you only use or disclose the barest minimum amount of PHI needed to accomplish a specific objective. This applies to both electronic and paper records containing PHI.
In keeping with this principle, you'll need to create a company-wide policy to limit PHI access, use, and disclosure at all levels.
Now, let's look at how to draft one of the most important legal documents to ensure HIPAA compliance: A Privacy Policy.
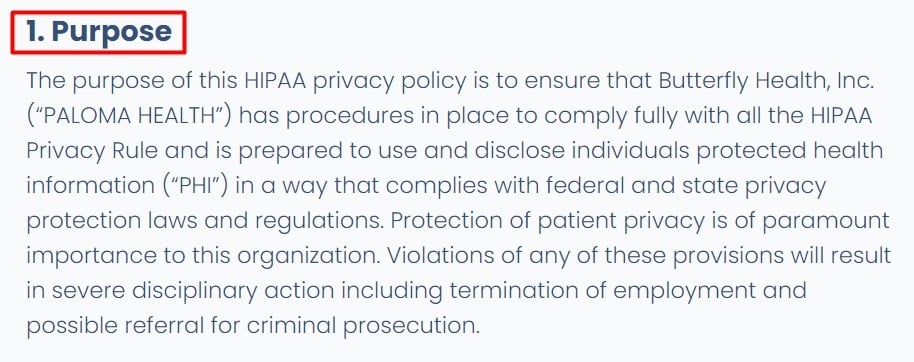
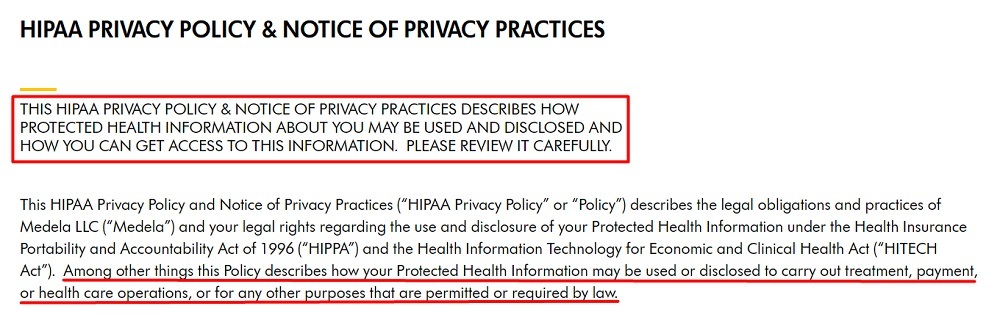
The Health Insurance Portability and Accountability Act (HIPAA) and Your Privacy Policy

One of the best ways to ensure HIPAA compliance is to maintain a comprehensive and easy-to-understand Privacy Policy on your website or app.
This document is vital for complying with the Privacy Rule's mandate to implement policies and procedures for safeguarding PHI.
What's more, it helps build trust and credibility for your organization - two values that are paramount when handling sensitive data like medical records and other health information.
Your Privacy Policy must include a few essential clauses to comply with HIPAA's rules, which we'll review below.
Introductory Clause
An introductory clause is an integral component of any good Privacy Policy. Here, you'll need to provide an overview of what the policy entails. In this case, it will be how you collect, use, and disclose PHI to facilitate your business operations.
Here's how PALOMA HEALTH presents this clause at the beginning of its HIPAA Privacy Policy:
And here's how Medela displays this clause:
Uses and Disclosures of PHI
Next, you need to explain how you intend to use patients' PHI and with whom you may share it. It's a best practice to be as transparent and detailed as possible when describing this clause in your Privacy Policy.
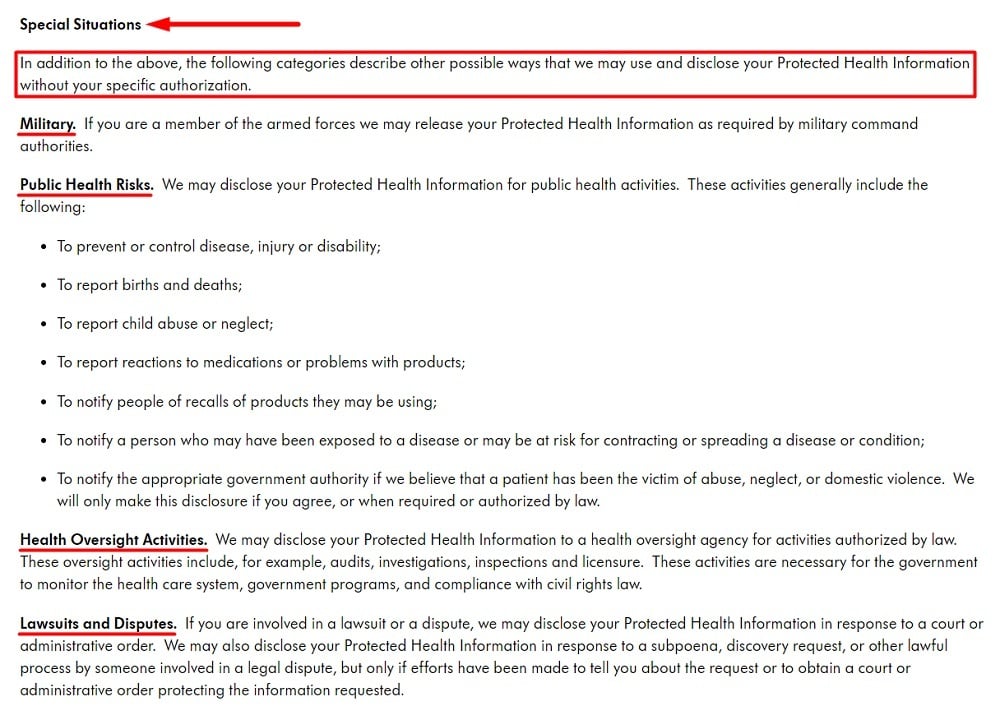
You should also outline special situations where you may use or disclose PHI without a patient's authorization, such as when required by law.
Once again, Medela does this well. Here's how it explains its key uses and disclosures of PHI:
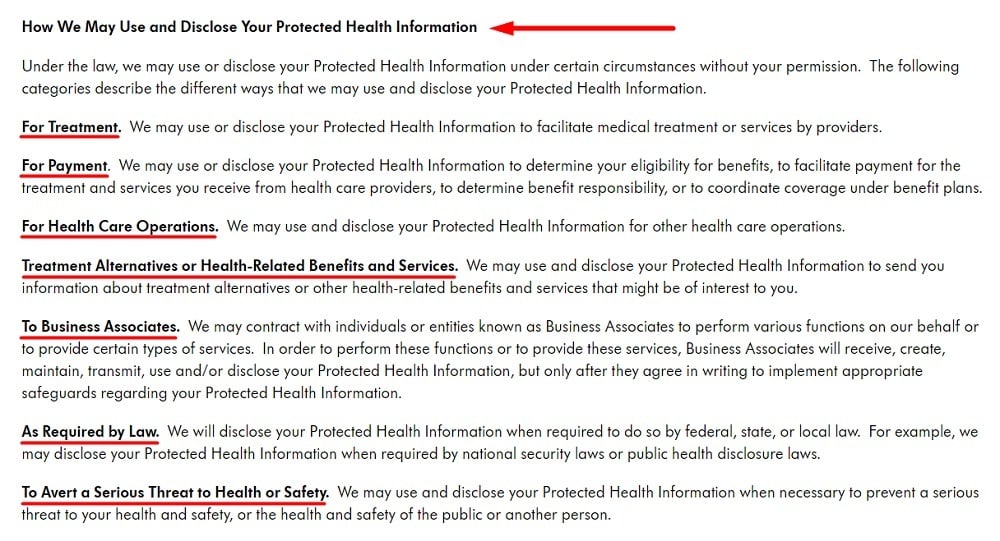
And here's how Medela outlines special situations where it may use or disclose PHI without patients' permission:
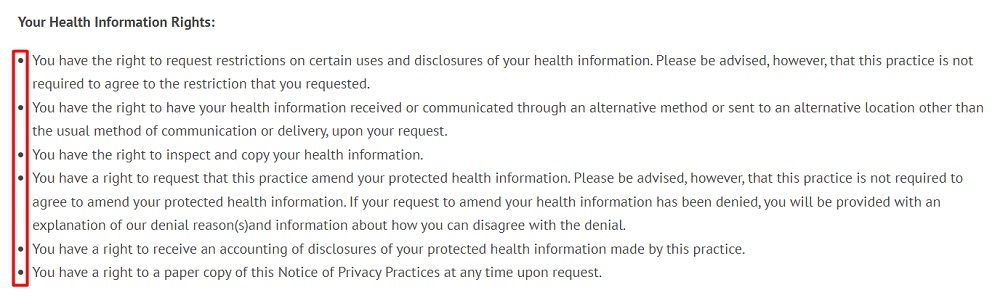
Individual Privacy Rights
As noted earlier, HIPAA's Privacy Rule grants individuals several rights over their PHI. Your Privacy Policy must mention these rights in a simple, user-friendly way and explain how individuals can exercise them and under what circumstances.
Here's how South End Eye presents individuals' privacy rights in a simple and concise form, using a bullet list to enhance readability:
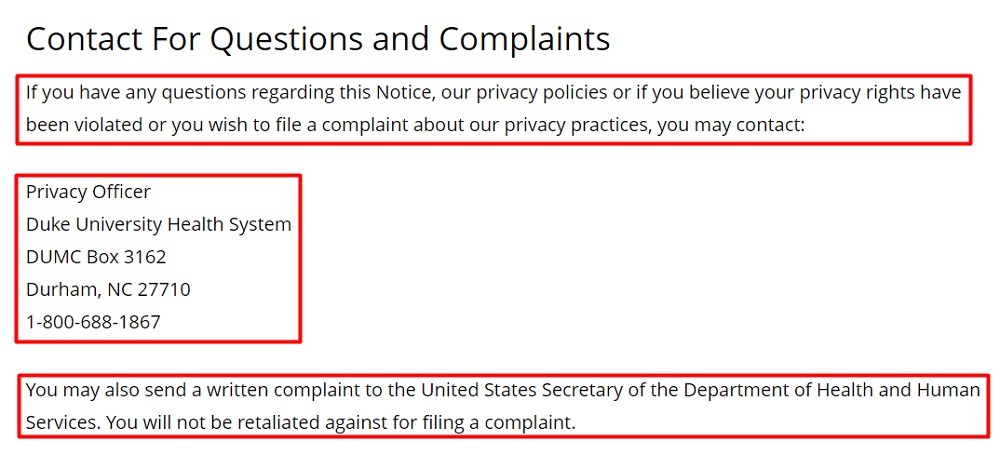
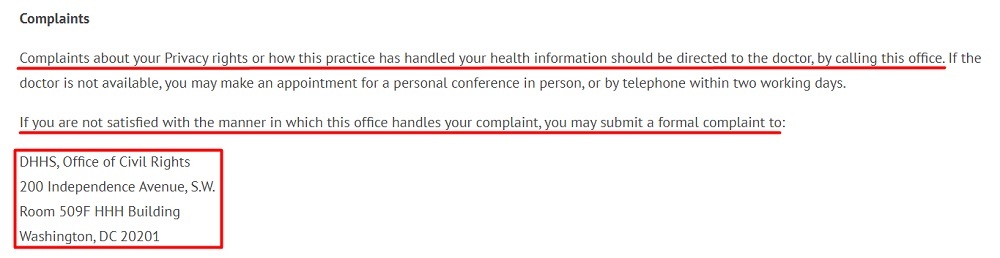
Contact Information for Questions and Complaints
Individuals have the right to ask questions about how you use or disclose their PHI.
They also have the right to file a complaint if they believe your organization has violated their HIPAA rights. They can send this complaint to your organization, and if not satisfied with the results, escalate it to the HHS Office for Civil Rights (OCR).
Your Privacy Policy must explain this information clearly and include your contact details to address questions and complaints like here Duke Health does here:
Here's another example from South End Eye addressing this information in its Privacy Policy:
Now that we've covered the major requirements under HIPAA, you may be wondering what happens if you don't comply. Well, let's take a look.
Penalties for Non-Compliance with HIPAA

Non-compliance with HIPAA's rules can result in severe penalties for both covered entities and their business associates.
As the body responsible for enforcing HIPAA penalties, the HHS Office for Civil Rights (OCR) imposes different types of penalties for different levels of violations.
They include:
- Civil penalties
- Corrective Action Plans (CAPs)
- Criminal penalties
For civil penalties, the OCR sets out four tiers of fines depending on the severity of the infringements and how fast the violation is corrected.
As of March 17, 2022, the inflation-adjusted values for each tier of HIPAA penalties, as released by the HHS, are as follows:
| Penalty Tiers | Offense | Minimum Penalty Per Violation | Maximum Penalty Per Violation | Calendar Year Cap |
| Tier 1 | Accidental violation | $127 | $63,973 | $1,191,173 |
| Tier 2 | Reasonable Cause | $1,280 | $63,973 | $1,191,173 |
| Tier 3 | Willful neglect - Corrected within 30 days | $12,794 | $63,973 | $1,191,173 |
| Tier 4 | Willful neglect - Not corrected within 30 days | $63,973 | $1,919,173 | $1,191,173 |
In addition to the civil penalties, the OCR may compel violators to implement a Corrective Action Plan (CAP). A CAP is a detailed plan outlining the steps a business must take to correct HIPAA violations and prevent them from happening again.
Finally, HIPAA violations may result in criminal charges for covered entities that knowingly collect or disclose PHI in violation of HIPAA rules.
The U.S. Department of Justice (DOJ) regulates HIPAA criminal penalties and may impose fines of up to $250,000 and up to ten years in prison, depending on the severity of infractions.
Summary
HIPAA is a federal law that sets national standards for the privacy and security of Protected Health Information (PHI) in the United States.
Among other things, HIPAA grants individuals more control over their health information, helps maintain health insurance coverage for workers between jobs, and modernizes the flow of PHI in the U.S. healthcare sector.
Note that PHI is any information that identifies an individual and relates to their health.
HIPAA applies to two major groups that handle PHI: Covered Entities and Business Associates.
Under HIPAA, covered entities include healthcare providers, health plans, and healthcare clearinghouses. On the other hand, business associates are third-party organizations that provide PHI-driven services to covered entities.
When handling PHI, covered entities and their business associates must observe four major HIPAA rules, including:
- The Privacy Rule
- The Security Rule
- The Breach Notification Rule, and
- The Enforcement Rule
As a covered entity or business associate, you must take the following steps to comply with these rules:
- Implement sufficient data security safeguards to protect PHI
- Observe and help exercise individual rights under HIPAA
- Conduct regular risks assessment programs
- Notify affected individuals and appropriate authorities of data breaches
- Provide a Notice of Privacy Practices (NPP)
- Set up Business Associate Agreements (BAAs) for all partnerships involving PHI
- Limit the use and disclosure of PHI to what is absolutely necessary
- Maintain a HIPAA-compliant Privacy Policy that includes the essential clauses identified above
Remember, the penalties for non-compliance with HIPAA can be severe, including reputational damages, civil penalties, and even criminal prosecution.
All US Privacy Laws
Want to read more about privacy laws in the USA? Start here:
| COPPA: Children's Online Privacy Protection Act | Federal law that protects the privacy of children under 13 years of age when online or using a mobile app. |
| HIPAA: Health Insurance Portability and Accountability Act | Federal law that protects the privacy of health information of individuals. |
| California CalOPPA: California Online Privacy Protection Act | California law that requires commercial websites to properly display a compliant Privacy Policy. |
| California CCPA: California's Consumer Privacy Act | California law that gives consumers many privacy rights while putting transparency obligations on businesses. |
| California CPRA: California's Privacy Rights Act | California law that expands the CCPA and gives consumers additional rights. |
| Virginia VCDPA: Virginia's Consumer Data Protection Act | Virginia law that allows users to opt out of the sale of their personal data. |
| Maryland PIPA: Maryland's Personal Information Protection Act | Maryland law that requires businesses to keep personal information private and secured. |
| Utah UCPA: Utah's Consumer Privacy Act | Utah law that provides a range of consumer privacy rights, including the right to data portability. |
| Connecticut CTDPA: Connecticut's Personal Data Privacy and Online Monitoring | Connecticut law that places transparency requirements on businesses while granting consumers rights over their personal data. |
| Colorado CPA: Colorado's Privacy Act | Colorado law that grants privacy rights to consumers while dictating how businesses can collect and process personal data. |
| Florida FPPA: Florida's Privacy Protection Act | Florida law that lets consumers control how their personal data is used, while requiring businesses to be more transparent. |

Comprehensive compliance starts with a Privacy Policy.
Comply with the law with our agreements, policies, and consent banners. Everything is included.