The Internet of Things (IoT) has the potential to make people's lives easier and more efficient, but the trade-off could be the potential issues that could arise over the security of collected personal data.
If you're developing IoT devices, you must address these privacy issues when designing your device. Do so despite the current lack of an up-to-date guiding law in the area.
IoT devices need the Privacy Policy agreement if the device collects personal information from users.
There are two main reasons why you need a Privacy Policy:
✓ Privacy Policies are legally required. A Privacy Policy is required by global privacy laws if you collect or use personal information.
✓ Consumers expect to see them: Place your Privacy Policy link in your website footer, and anywhere else where you request personal information.
Generate an up-to-date 2024 Privacy Policy for your business website and mobile app with our Privacy Policy Generator.
One of our many testimonials:
"I needed an updated Privacy Policy for my website with GDPR coming up. I didn't want to try and write one myself, so TermsFeed was really helpful. I figured it was worth the cost for me, even though I'm a small fry and don't have a big business. Thanks for making it easy."
Stephanie P. generated a Privacy Policy
Recently a report was released by the FTC (Federal Trade Commission) which provides guidance for companies and manufacturers on how they can build privacy and security measures into their devices.

Without proper privacy practices, the FTC Chairwoman Edith Ramirez believes that consumer confidence could be damaged:
The only way for the Internet of Things to reach its full potential for innovation is with the trust of American Consumers. We believe that by adopting the best practices we've laid out, businesses will be better able to provide consumers the protections they want and allow the benefits of the Internet of Things to be fully realized.
The importance of gaining this trust can be best seen in the example of the frenzy that was created over a line from Samsung's Privacy Policy for their smart TV:
Please be aware that if your spoken words include personal or other sensitive information, that information will be among the information captured and transmitted to a third party.
The spoken words needed to use the TV are those for using the TVÕs functions, such as changing the channel, it is easy to see that users may be concerned that any other information spoken around the TV may also be stored.
Recommendation 1: Data minimization
FTC's suggestion is that you limit the user data that you collect and how long you keep it for. This is known as data minimization.
This practice essentially reduces two risks in one:
- If your company is not storing large amounts of data it is less of a target to data thieves or hackers.
- The less data that is collected and the less time it is stored for the lower the chance that the data will be used in ways that contradict the users' expectations.
The FTC is flexible as to how you can approach data minimization.
You can choose collect no data, collect data limited to the categories required to provide the service offered by the device, collect less sensitive data, or de-identify the data you collect.
Recommendation 2: Notice and choice
Another guideline by the FTC is that you notify your users and give them choices about how their information will be used, especially when the data collection may go beyond the users' reasonable expectations.
While it can be difficult in an IoT context to notify users of your company's privacy practices and any changes you do to your Privacy Policy agreement, it's essential to do this.
The FTC made it clear that putting your Privacy Policy on your website is not sufficient notification to your users of your privacy practices. Instead, the FTC recommends that you find a way to meaningfully present privacy notices and choices to customers, including in the set-up or purchase of the IoT device itself.
With the ever-developing world of IoTs notification will become more and more difficult and the FTC has acknowledged that there can be no one-size-fits-all approach, so there are other ways to make your users feel more at ease with the use of their data:
- Always make personal information anonymous in a way that makes re-identifying the user impossible. This removes the user's concerns about the nature and use of data collected.
- Monitor data transmissions so that misuses can be blocked.
What's clear from the FTC's report is that you must consider the privacy of the data when manufacturing IOT devices, but you must also balance this with the potential to collect valuable data.

Europe's Article 29 Working Party has published an opinion, called Opinion 8/2014 on the on Recent Developments on the Internet of Things, that focuses on:
- Wearable Technology: clothes, watches, contact lenses with ensors, microphones with cameras embedded, and so on
- Quantified Self: pedometers, sleep monitors, and so on
- Home Automation: connected households using smart fridges, smart lighting and smart security systems, and so on
Europe's Article 29 Working Party is the same entity that issued a guidance to Google to ensure that Google is in compliance with EU data protection laws.
If you're a designer or developer developing a new IoT device within the categories mentioned above, the opinion by the Article 29 Working Party would be useful to you as guidance when implementing your first privacy practices.
The Working Party found the following issues with the current IoT devices:
- Users do not have control over the communication of their data
- Consent given by users badly implemented
- The use of the collected data can go beyond the reasons for which it was originally collected or beyond what the Privacy Policy agreement mentions
- Previous activities that were private can become identifiable or public when IoT devices are used or connected
- Limitation imposed on removing anonymous data while using the IoT device
- Risks regarding the security of data collected
Based on their guidance document, here's what the Article 29 Working Party suggests to IoT developers:
- Users must be able to access, view and remove the data you collect from them. Users should be able to disconnect their IoT devices when they want to do so.
- Consent of users must be gained to store their personal data on the IoT device.
Here's are the current steps you can follow to increase your chances of compliance:
- Analyze the impact of how your IoT device designed on the privacy of users using it
- Design your device is such ways that raw data will be deleted as soon as it is no longer required for processing
- Learn the principles of Privacy by Design and apply them when you design your device
- Users should have control over the IoT device (connect and disconnect as they want to do so) and control over the collected data (view or delete data)
- Make sure the information you collect from users is easily accessible by users
- The consent users give you must be freely given, explicit and informed. Users should have the ability to withdraw their consent if they want to do so.
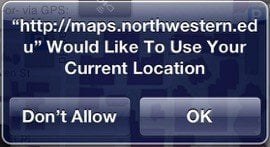
Here's how an iOS app would ask users to provide their location:
Here are some of these principles that you can follow:
- The principles of the Privacy by Design must be at every step of your device development. Security regarding the data collected from users should be built in, and not be an afterthought.
- Inform users about the information you'll collect, which information is personal and which is not, and so on.
You can do so through the privacy Policy agreement that users can read and agree to before they start using the device.
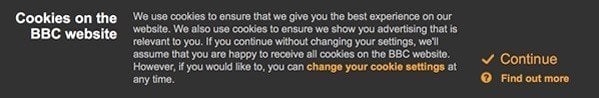
Here's how BBC.co.uk notifies users about their cookies usage to comply with EU Cookies Directive:
- Always keep in touch with your users, especially if the IoT device doesn't have a screen that would allow you to communicate with your users.
Ask users to provide you with a contact information - email address, mail address - that you can use to inform users about upcoming changes.
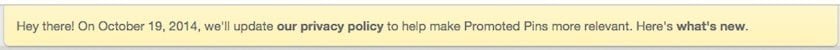
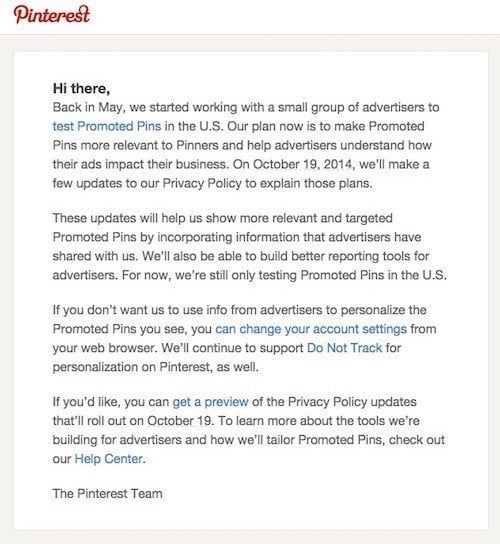
Here's how Pinterest notifies users about upcoming changes to their Privacy Policy:
- Train your employees so that security over the users personal data is managed appropriately at all levels of your business
- Consider adopting a data minimization policy. In other words: don't collect more data than you need.
- Ask users for location tracking
- Give your users the right to access and export their data
- Have a method of notifying your users when vulnerabilities are discovered so they can update or disconnect their devices.
Here's the email Pinterest sent out when their legal agreement was being updated:
If you are also developing a mobile app for the IoT device, follow these tips too:
- Notify users that personal data might be collected through the IoT device and the mobile app. Do so through your Privacy Policy agreement.
- Make sure that users can access and have control over the data you've collected through the IoT device on the mobile app.

Comprehensive compliance starts with a Privacy Policy.
Comply with the law with our agreements, policies, and consent banners. Everything is included.