Any business that operates from within Australia or caters to residents of Australia needs to understand and abide by Australia's privacy laws. Maintaining an Australian Privacy Policy is an excellent way to make sure that your business is in compliance with Australia's privacy legislation.
This article will teach you everything you need to know about Australia's foremost privacy law, how to write a compliant Australian Privacy Policy, and how to display and get agreement to your Australian Privacy Policy.
- 1. The Australian Privacy Act of 1988
- 2. The 13 Australian Privacy Principles
- 2.1. 1. Be Transparent
- 2.2. 2. Allow Anonymity
- 2.3. 3. Limit the Collection of Solicited Information
- 2.4. 4. Handle Unsolicited Information With Care
- 2.5. 5. Let Users Know How You are Collecting Their Data
- 2.6. 6. Inform Users How You Use or Share Their Data
- 2.7. 7. Limit the Use of Collected Information for Direct Marketing
- 2.8. 8. Be Intentional When Sharing Information Across Borders
- 2.9. 9. Follow Steps for Using Government Related Identifiers
- 2.10. 10. Only Collect Valid Information
- 2.11. 11. Keep Collected Data Safe
- 2.12. 12. Give Users a Way to Access Their Information
- 2.13. 13. Give Users a Way to Change Their Information
- 3. How to Write a Compliant Australian Privacy Policy
- 3.1. What Kinds of Information You Collect
- 3.2. How You Use the Information You Collect
- 3.3. How You Collect Personal Information
- 3.4. Who You Share Information With
- 3.5. How Users Can Access or Edit the Information You Collect
- 3.6. How Users Can Report a Privacy Violation
- 3.7. How You Keep the Information You Collect Safe
- 3.8. How Users Can Contact You
- 4. How to Display Your Australian Privacy Policy
- 4.1. Website Footer
- 4.2. Account Login Page
- 4.3. Email Sign-Up Form
- 4.4. Checkout Page
- 4.5. Mobile App
- 5. How to Get Agreement to Your Australian Privacy Policy
- 6. Summary
The Australian Privacy Act of 1988
The primary Australian privacy law that businesses need to be aware of is the Australia Privacy Act of 1988 and its 13 Australian Privacy Principles (APPs).
Australia's Privacy Act of 1988 regulates how organizations collect, use, store, and disclose individuals' personal information. The Privacy Act defines personal information as any identifying information about an individual.
The 13 Australian Privacy Principles

The 13 Australian Privacy Principles serve to protect individuals' personal information as well as hold organizations accountable for how they handle the data that they collect. If your business is found to be in violation of any of these Principles you can face financial penalties or regulatory action.
Penalties for intentional or repeated violations are the higher amount of $50 million AUD per violation or three times the value of the benefit that the organization received from the violation.
An easy way to ensure that you are following these Principles is to incorporate them as part of your Privacy Policy.
Here are the 13 Privacy Principles and examples from real Privacy Policies showing how to comply with them.
1. Be Transparent
You should be transparent in how you manage personal information, and you can do this by maintaining a clearly written and up to date Privacy Policy on your website and apps.
The Introduction to BHP's Privacy Policy is open and transparent about how the company handles users' personal information:
2. Allow Anonymity
You should make sure to give users the choice of remaining anonymous or allow them to use a pseudonym.
Ramsay Health Care's Australia Privacy Policy lets users know that they have the option of anonymity when interacting with the company:
3. Limit the Collection of Solicited Information
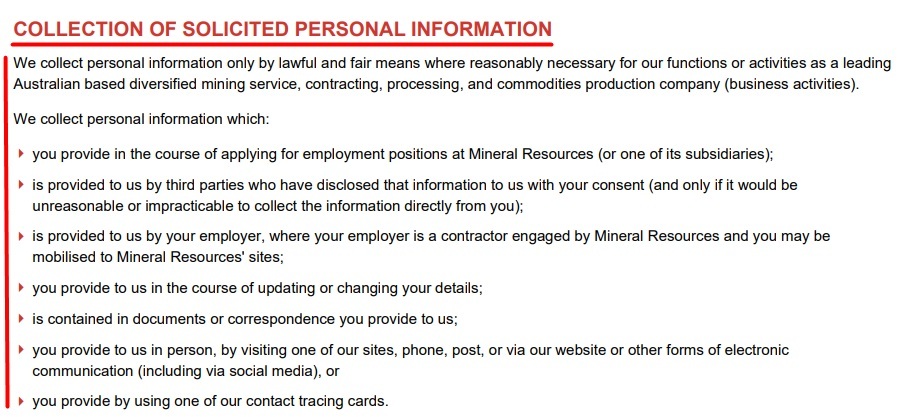
It's important to only collect solicited personal information under certain circumstances.
Mineral Resources' Privacy Policy lets users know how and what types of solicited personal information it collects:
4. Handle Unsolicited Information With Care
You will need to have a process for dealing with unsolicited personal information in a lawful and secure manner.
Westfield's Privacy Policy explains how it de-identifies or destroys any unsolicited information it receives from other people after first attempting to contact the individual the information identifies:
5. Let Users Know How You are Collecting Their Data
You should inform users about the specifics of the data collection as soon as possible when collecting their personal information. Disclose the methods you use to collect data.
Newcrest uses its Privacy Policy to inform users as to how it collects their personal information.
6. Inform Users How You Use or Share Their Data
It's crucial to let users know under what circumstances you use or share the data you collect.
WiseTech Global's Privacy Policy explains how it processes the personal information it collects when users visit its website.
7. Limit the Use of Collected Information for Direct Marketing
You will need to meet certain conditions in order to use any information you collect for direct marketing.
Organizations cannot use or disclose individuals' personal information for direct marketing, except under specific circumstances, outlined below:
-
Information Collected Directly and Reasonably Expected Use
The organization collected the information directly from the individual and the individual could reasonably expect that the information would be used for direct marketing and the organization provides a way for the individual to opt-out of receiving direct marketing communications from the organization.
The individual must be opted-in to receiving direct marketing communications in order for the organization to legally use their personal information for direct marketing purposes.
-
Information Collected Directly or Indirectly and Unexpected Use
An organization that has collected personal information from an individual that they wouldn't reasonably expect to be used for direct marketing or that has collected personal information about an individual from a different party can still use the information for direct marketing as long as it meets the following conditions:
- The individual must consent to having their information be used for direct marketing or it's not possible to obtain their consent
- The organization must provide a way for the individual to opt out of having their personal information be used for direct marketing
- The organization must include a statement in each form of direct marketing communication with the individual letting them know either how to opt-out or letting them know that they have the right to opt out, and
- The individual must not have opted-out of using their personal information for direct marketing purposes
-
Organizations that Collect Sensitive Personal Information
Organizations that collect sensitive personal information can use it for direct marketing as long as the individual it is collected from consents to having it used for that purpose.
-
Contracted Service Providers
Contracted service providers for Commonwealth contracts that collect personal information in order to fulfill the terms of a contract can use that information for direct marketing purposes.
The Collection, use, and disclosure of personal information for marketing clause of Suncorp's Privacy Policy describes how it uses the personal information it collects for marketing purposes, as well as how users can change their marketing preferences:
suncorp-privacy-policy-collection-use-disclosure-personal-information-marketing-clause
Suncorp Privacy Policy: Collection use and disclosure of personal information for marketing clause
8. Be Intentional When Sharing Information Across Borders
Before sharing information with any entity outside of Australia, an organization must first make sure that the entity it is sharing information with follows the Australian Privacy Principles.
The following exceptions apply to this rule:
- The entity receiving the information is legally obligated to follow privacy laws that protect personal information in a similar fashion to the Australian Privacy Principles.
- The individual consents to having their personal information disclosed.
- The information is legally required to be disclosed under Australian law or court order.
South32's Privacy Policy goes into detail about how it discloses and transfers the personal information it collects to other countries:
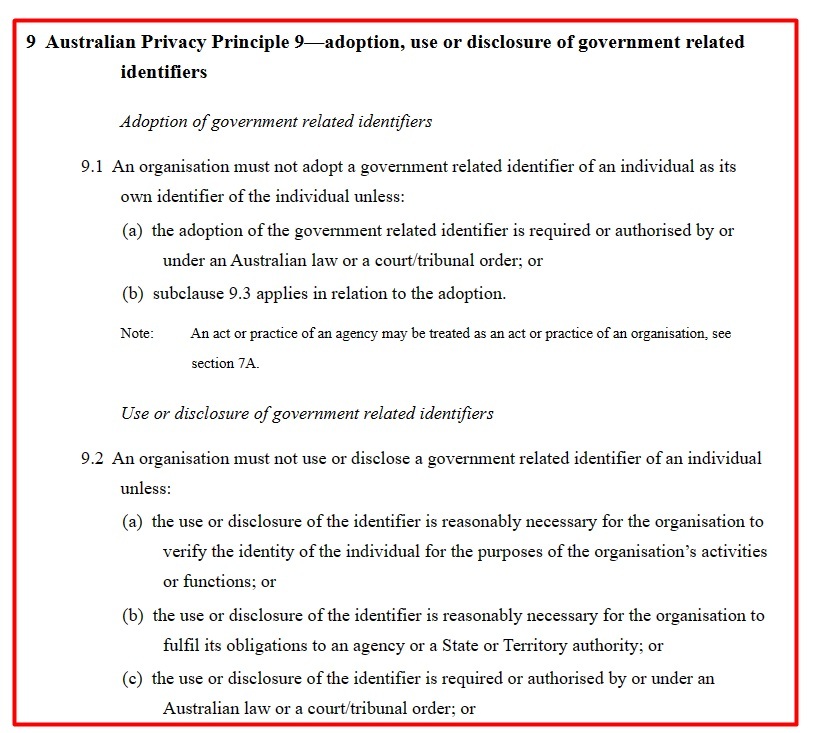
9. Follow Steps for Using Government Related Identifiers
In order to comply with the Australian Privacy Act, you will need to only use government related identifiers under specific circumstances.
The text of the Privacy Act of 1988 explains the exceptions to the government related identifier Principle:
10. Only Collect Valid Information
You will need to make sure that you have a system in place for ensuring that the information you collect is accurate.
Ampol's Privacy Policy lets users know that it takes steps to ensure that the information it collects is accurate, but that they should reach out if they need to change their information for any reason:
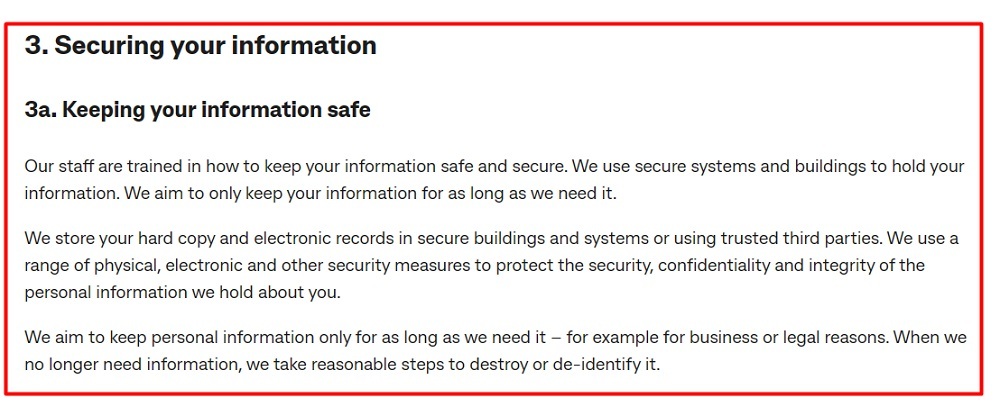
11. Keep Collected Data Safe
It is essential that you keep the information you collect secure. While you don't need to disclose your specific security measures, you do need to at least mention that you take steps to keep data safe.
Commonwealth Bank's Privacy Statement outlines the steps it takes to keep the information it collects safe, including training its staff, keeping its systems and buildings secure, and only storing information for as long as necessary:
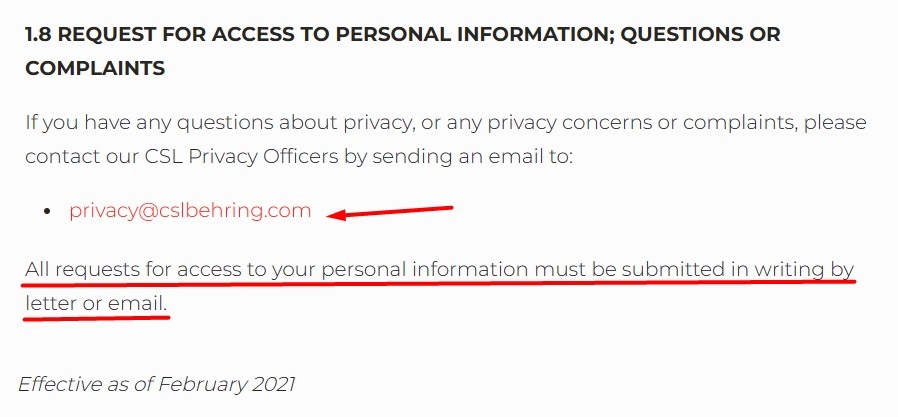
12. Give Users a Way to Access Their Information
Users need to have an easy way to access the personal data that you collect.
CSL's Privacy Policy includes its Privacy Officers' email address where users can send requests to access their personal information:
13. Give Users a Way to Change Their Information
You should maintain a method for users to modify their personal information. This can be by contacting you, or through a user account interface that allows users to edit their information on the spot.
This may depend on the nature of your platform and the information you collect. For example, if you don't allow user accounts or have a login feature, the only way users could change information would be by requesting you do it for them.
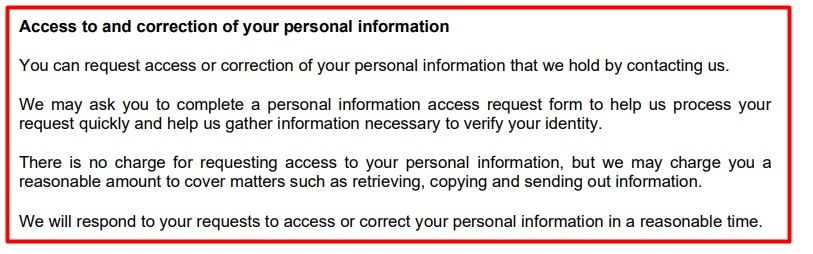
Insurance Australia Group's Privacy Policy lets users know that they should contact it if they need to make any changes to their personal information:
Remember: Complying with these 13 principles is mandatory if you fall under the scope of Australian privacy law.
Next let's look at what your Privacy Policy should look like when it comes to complying with Australian law.
How to Write a Compliant Australian Privacy Policy

One of the simplest ways to comply with the Australian Privacy Act and the APPs is to create and display a compliant Privacy Policy. You'll notice that many of the clauses outlined in the following section line up with the 13 principles noted in the previous section.
Your Australian Privacy Policy should include the following clauses in order to describe what steps you are taking to protect users' personal information and comply with the Australian Privacy Act.
Below we'll look at what clauses your Australian Privacy Policy should include, with examples of each.
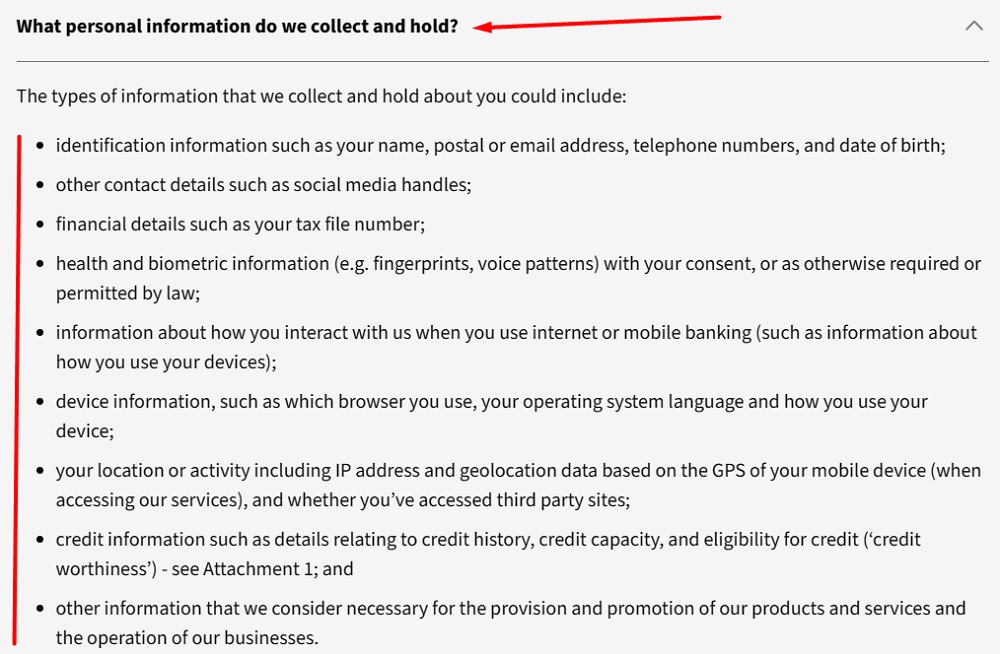
What Kinds of Information You Collect
This clause consists of a list of the types of personal information you collect.
The What personal information do we collect and hold? section of the National Australia Bank's Privacy Policy lets users know what kinds of personal information it collects:
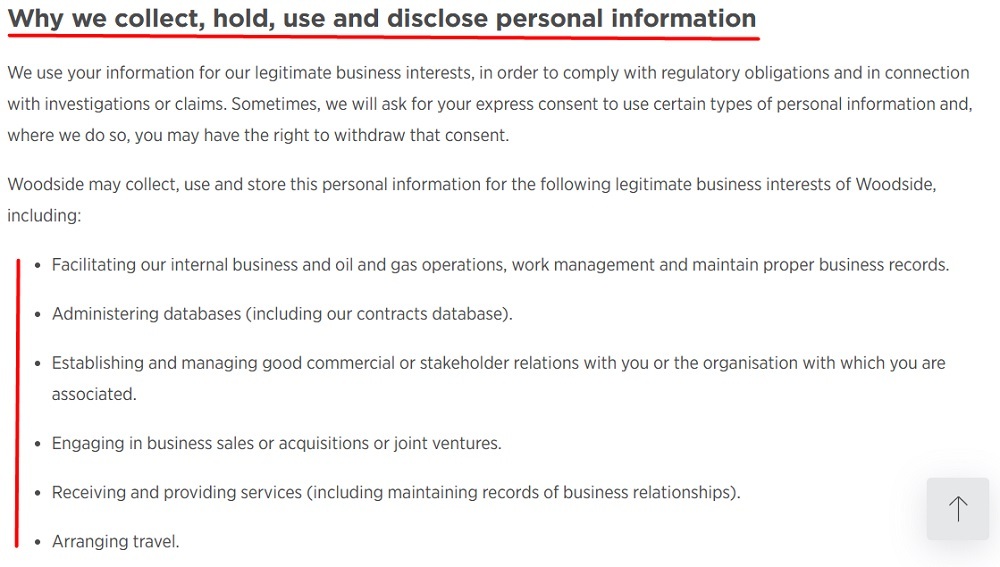
How You Use the Information You Collect
You should use this clause to describe what you do with the personal information you collect.
Woodside Energy's Privacy Statement describes the purposes for which it collects, holds, uses, and discloses personal information. Note that this is just an excerpt of the full list of uses of information:
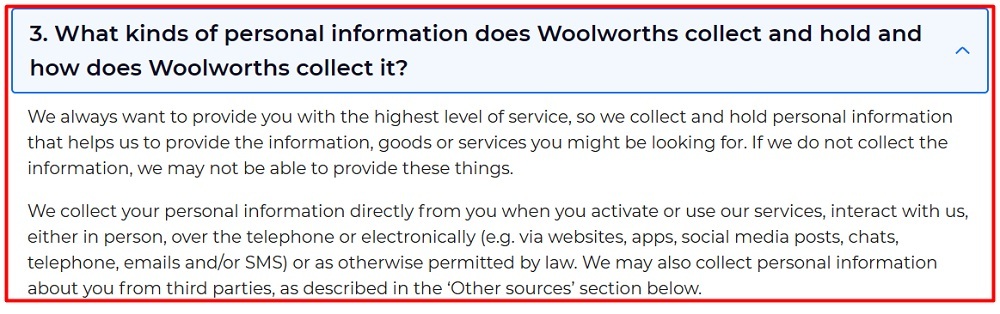
How You Collect Personal Information
Your Privacy Policy needs to explain how you collect personal information, whether directly, such as via email or subscription sign-up forms, or indirectly, such as through tracking or third party services.
Woolworths Group's Privacy Policy explains that it collects personal information from users both directly and via third parties:
Who You Share Information With
It's important to inform users about any third parties you share the personal information you collect with.
Atlassian uses the How we share information we collect clause of its Privacy Policy to explain that it shares the personal information it collects via its Services and with third parties:
How Users Can Access or Edit the Information You Collect
Your Privacy Policy should let users know how they can access and change their personal information.
Transurban's Privacy Policy includes a contact link that users can follow in order to gain access to their personal information:
How Users Can Report a Privacy Violation
This clause informs users how they can file a complaint if they believe that their privacy rights have been violated.
Aristocrat Leisure Limited's Privacy Policy includes a section under its Your Rights and Choices clause that informs users how they can file a complaint about how the company handles their personal information:
How You Keep the Information You Collect Safe
You should let users know what kind of security measures you employ to keep the personal information you collect safe.
Sonic Healthcare's Protecting your personal information clause goes into detail about the steps it takes to keep the information it collects secure:
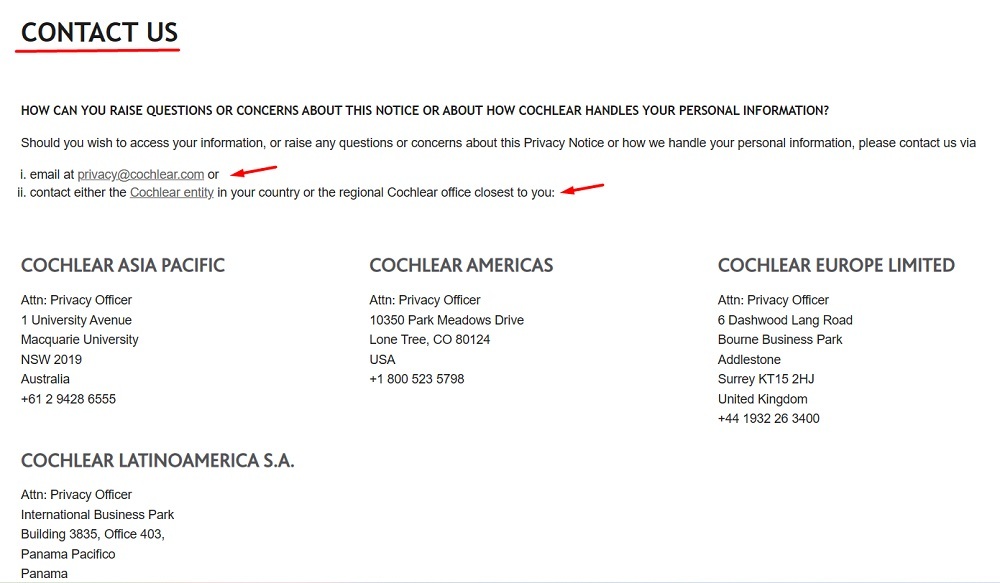
How Users Can Contact You
Your Privacy Policy should include up to date and accurate contact information for your company's appointed privacy officer. The more methods of contacting you, the better.
Cochlear puts its contact information at the end of its Privacy Notice, giving users the choice to either email it or call any of its international offices:
After you write a compliant Privacy Policy, you need to display it in a transparent, easy-to-see way so the public can access it at any time. Here are some best practice places and methods for displaying your Australian Privacy Policy.
How to Display Your Australian Privacy Policy

There are several places where businesses commonly display their Privacy Policy, including on their website footers and account login and checkout pages, as a part of their email or newsletter sign-up forms, and within their mobile apps.
Website Footer
Many businesses put links to their legal agreements in their website footer, which is a common enough placement that most users know to look there to find your Privacy Policy.
Ampol puts a link to its Privacy Policy at the bottom of its website, along with links to its contact information, Sitemap, and Terms of Use agreement:

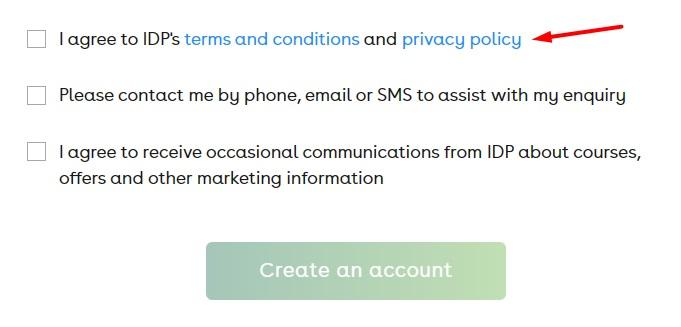
Account Login Page
Another popular place to put your Privacy Policy is on your membership login page, so that anyone who wishes to create or sign into an account has access to your privacy information before sharing information with you.
Users must tick a box agreeing to IDP Education's Privacy Policy before creating an account with the company. An "I Agree" checkbox is a great way to get compliant consent for your privacy practices:
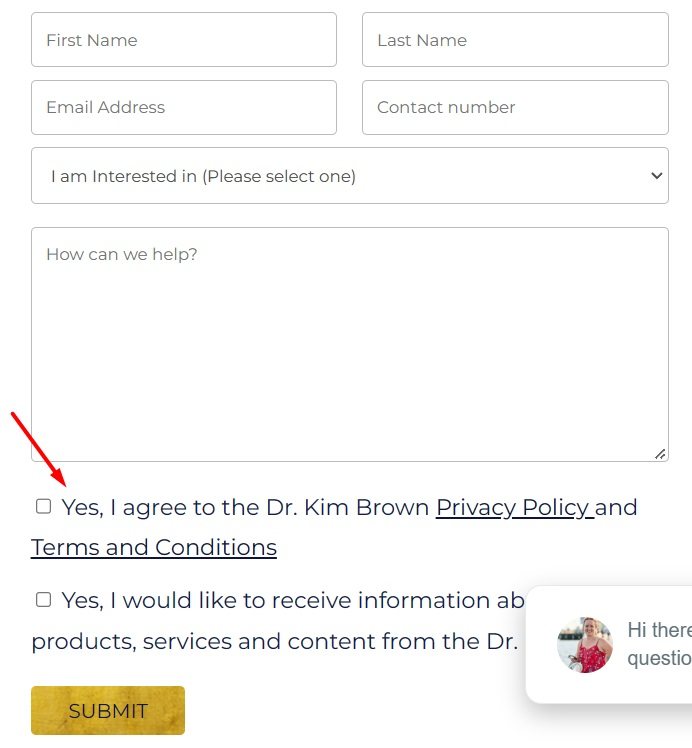
Email Sign-Up Form
Businesses that send out newsletters or marketing emails can include a link to their Privacy Policies as a part of their email sign-up forms.
Dr. Kim Brown includes a checkbox that users must click affirming that they have read her Privacy Policy before signing up to receive more information about her business:
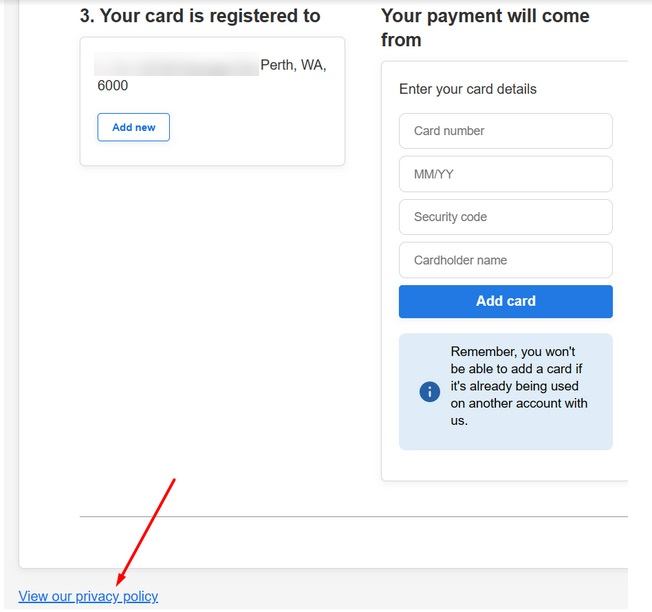
Checkout Page
If you have an ecommerce business, you can ensure that your customers have the opportunity to read your Privacy Policy by including a link to it on your checkout page.
Naked Wines' checkout page includes a link to its Privacy Policy below the area where consumers enter their payment info:
Mobile App
Any business with a mobile app can add a link to its Privacy Policy in its in-app About or other type of menu, as well as within a pop-up notification box.
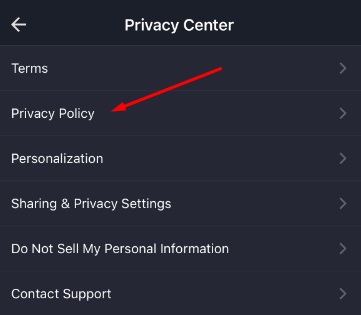
Here's an example of an in-app menu displaying a Privacy Policy link:
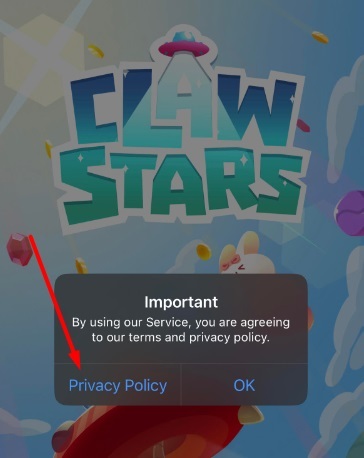
When users first download iCandy's Claw Stars game, they are greeted with a pop-up box that informs them that they must agree to its Privacy Policy and Terms before playing the game:
Just make sure that your Privacy Policy is always accessible at any time via a menu or within your website's footer. Users need to be able to access it at any moment.
How to Get Agreement to Your Australian Privacy Policy

One of the easiest ways to get agreement to your Australian Privacy Policy is through the use of checkboxes that users must check affirming that they have read and agree to your policy before taking further action on your website.
You can include checkboxes as a part of your account sign-up process, on your checkout page, or even as a pop-up box that users must click before navigating your website.
Examples of this were shown in the previous section, where users must check a box next to a statement and a link to the Privacy Policy.
Summary
The main Australian privacy law is the Australian Privacy Act of 1988. Any organization that operates out of Australia or does business with Australian citizens needs to make sure that they adhere to the Act's 13 Australian Privacy Principles.
One of the easiest ways to comply with the Australian Privacy Act is to make sure that your business has a compliant Privacy Policy. To write a compliant Australian Privacy Policy, you will need to make sure that it includes the following clauses:
- A statement describing the steps you are taking to comply with existing privacy legislation
- What kind of information you collect
- How you use the information you collect
- How you collect personal information
- What third parties you share the information you collect with
- How users can access and change their personal information
- How users can report a suspected privacy violation
- Security measures you take to keep the information you collect safe
- Your contact information
There are several places that businesses commonly display their Australian Privacy Policies, including on their website footers, on their account login and ecommerce checkout pages, and within their apps.
In order to ensure that users agree to your Australian Privacy Policy, you can use checkboxes that users must check signifying that they agree to your terms before signing up for an account or newsletter, making a purchase, or using your website or app.

Comprehensive compliance starts with a Privacy Policy.
Comply with the law with our agreements, policies, and consent banners. Everything is included.