Cookies have been used extensively since the mid-1990s by operators of websites. These small files that get placed on your computer or mobile device were at one point in time the choice tool used for creating custom and relevant online advertising, and for tracking certain usage habits of visitors to a website.
However, times have changed and cookies have crumbled.
In 2009, the European Union changed their influential ePrivacy Directive 2002/58/EC to place cookies under the scope of strict European data protection rules and regulations.
This started a legal requirement that before cookies could be placed on a user's machine, the user must give explicit consent to allow this to happen. Many companies did this through a Cookies Policy and a notice. Many users refused to give consent, and cookies got a bad reputation as being invasive and intrusive.
This is the EU Cookies Directive, also called the EU Cookies Law.
Start generating the necessary legal agreements for your website or app in minutes with TermsFeed.
We also offer different solutions and tools for your website or app:
- Privacy Consent (Cookie Consent). A cookie consent solution to comply with CCPA/CPRA, GDPR, ePrivacy Directive.
- CCPA/CPRA Opt-Out. A free CCPA/CPRA opt-out solution to allow visitors to opt-out from personalized ads and comply with CCPA/CPRA.
- "I Agree" Checkbox. A free solution to enforce your legal agreements.
What is device fingerprinting?
A modern technique that operates similarly to cookies is now gaining momentum as the new tracking method of choice.
This method is known as device fingerprinting.
Device fingerprinting is basically the collection of a variety of data about a user's device and the way that device is used. The data together forms a unique profile or "fingerprint" for the device.
These bits of information include operating system information, browser versions, and plugins being used, time zone location, IP addresses, and other related characters of the device.
Here's what the MobileAppTracking SDK collects:
- Country Code
- Device Brand
- Device Model
- Device Carrier
- IP Address
- Language
- OS Name
- OS Version
- Timestamp
Cookies vs. device fingerprinting
Cookies differ from device fingerprinting in that cookies are placed on a device and are then tracked. These cookies expire and can be deleted by users, making them somewhat unreliable and inconsistent.
Device fingerprinting is far more reliable and consistent. Fingerprints update themselves as changes are made to a device, and all of a user's information remains in that one fingerprint rather than in a number of different cookies.
Device fingerprints have much more longevity and stability, which makes them a better choice for websites or mobile apps looking to track user data.
The Article 29 Working Party, which is made up of representatives of each of the EU Member States Data Protection Authorities, has been pushing to have device fingerprinting made subject to the same EU data protection requirements and regulations as cookies.
While these recommendations are not binding, they are highly recommended. History of legislation has shown that opinions of the Article 29 Working Party are often turned into future regulations and should not be disregarded but rather treated as requirements.
Before you implement device fingerprinting
Here are a few suggestions to follow before you implement device fingerprinting:
- A user must give explicit consent prior to a device being fingerprinted for any advertising, market research, or website analytics purposes
- When a website or mobile app is seeking this consent, they must provide all users with very detailed but clear information about the fingerprinting that will be done, including what data will be collected, how that data will be used, and why this data is being used in such a manner
Users should be given the ability to opt out of having a device fingerprinted initially, and be given information on how to revoke consent in the future if so desired.
This is especially important since, unlike cookies, this fingerprinted information cannot just be deleted or blocked from the browser by the user.
Exceptions to obtaining consent
There are a few exceptions to the required consent. These exceptions are as follows:
- Consent to fingerprint a device is not necessary if the information gathered during fingerprinting is required to allow the device to access an electronics communication network and is used for nothing else.
- Consent to fingerprint a device is not necessary if the information gathered during fingerprinting is required in order to customize a user interface to a specific device.
For example, different devices have different video capabilities and a website with video content may need to gather the data about a specific device in order to optimize the videos for playback on that device.
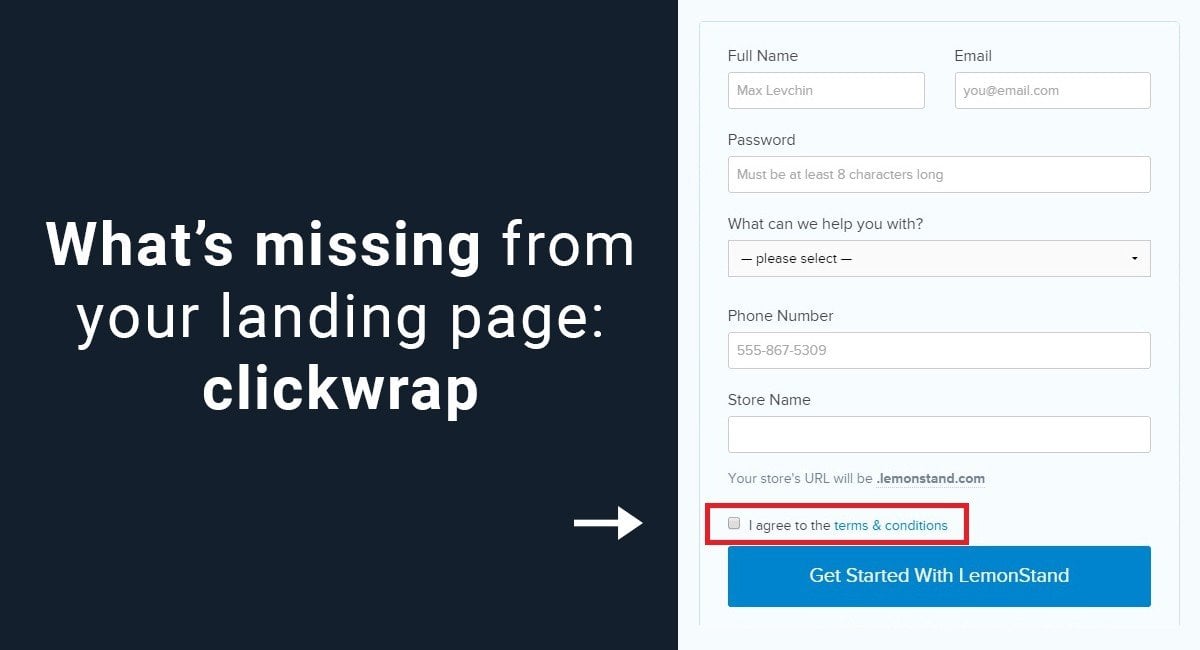
Obtaining consent with click-wrap
The clickwrap method is the most legally secure and favored method of obtaining explicit consent to fingerprinting a device of a user of your website or mobile app.
The "Browsewrap vs. Clickwrap" guide has more examples of clickwrap best practices.
Below is an example of a clickwrap method of obtaining consent on the Terms of Service of Engine Yard:

To use the clickwrap method, when a user visits your site or uses your mobile app for the first time, and before any fingerprinting takes place, make the user click on a box or a link that says he/she gives you consent.
Provide a link to your Terms of Use (also known as Terms & Conditions or Terms of Service) and Privacy Policy where you explicitly explain how, why, and when fingerprinting will occur and what you will do with the data collected.
Methods that are not clickwrap
While some website or mobile apps may place a small banner in a header or footer with a link to the terms of use and Privacy Policy, as well as language that alerts a user to the fact that device fingerprinting will occur if the user continues to use the site, this is not a good way of giving notice and obtaining actual consent.
The banner may be missed by the user.
Below is an example of a banner notice on cookies usage that may not be quite thorough enough used by Debenhams:
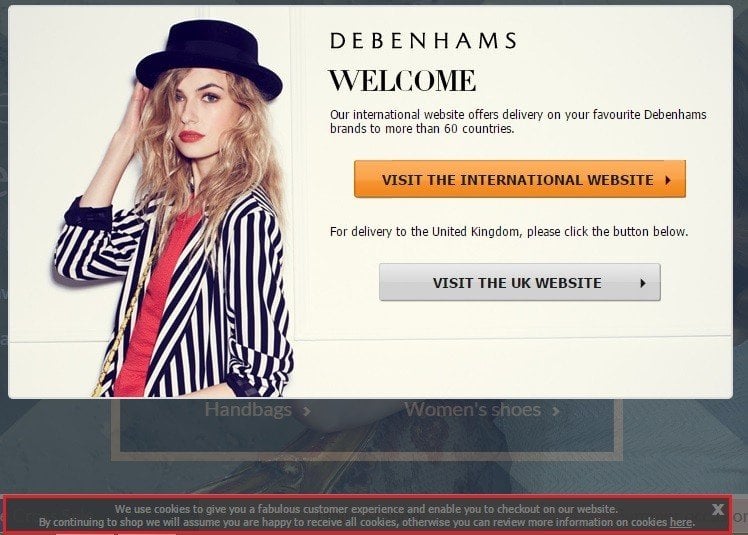
If the banner must be closed in order for a user to continue using the website or mobile app, that would be one step closer to being considered explicit consent; however, it still isn't a perfect method for obtaining consent.
When your website or mobile app conducts device fingerprinting and collects data from users, always provide as much specific information about this data collection as possible in a Privacy Policy and terms of use information page, and obtain consent from the user in the clearest and overt way as possible to ensure legal compliance.

The first step to compliance: A Privacy Policy.
Stay compliant with our agreements, policies, and consent banners — everything you need, all in one place.