The word "processing" appears in the EU General Data Protection Regulation (GDPR) over 630 times. The law features seven "principles of data processing." It requires companies to ensure the "resilience of processing systems." It even proclaims that "the processing of personal data should be designed to serve mankind."
Processing personal data is what the GDPR is all about. But have you ever stopped to consider what "processing" actually means?
The easy answer is that processing means "everything." It's hard to imagine an action you could take in relation to personal data that wouldn't qualify as "processing" it. But for anyone who really wants to understand their obligations under the law, this answer won't be enough.
Let's take a detailed look at the sorts of activities that count as processing under the GDPR.
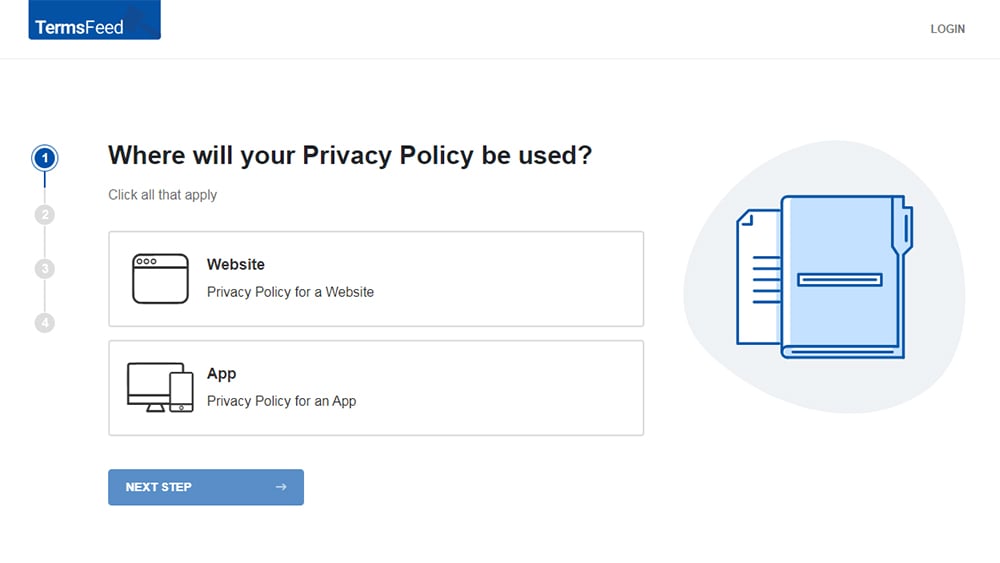
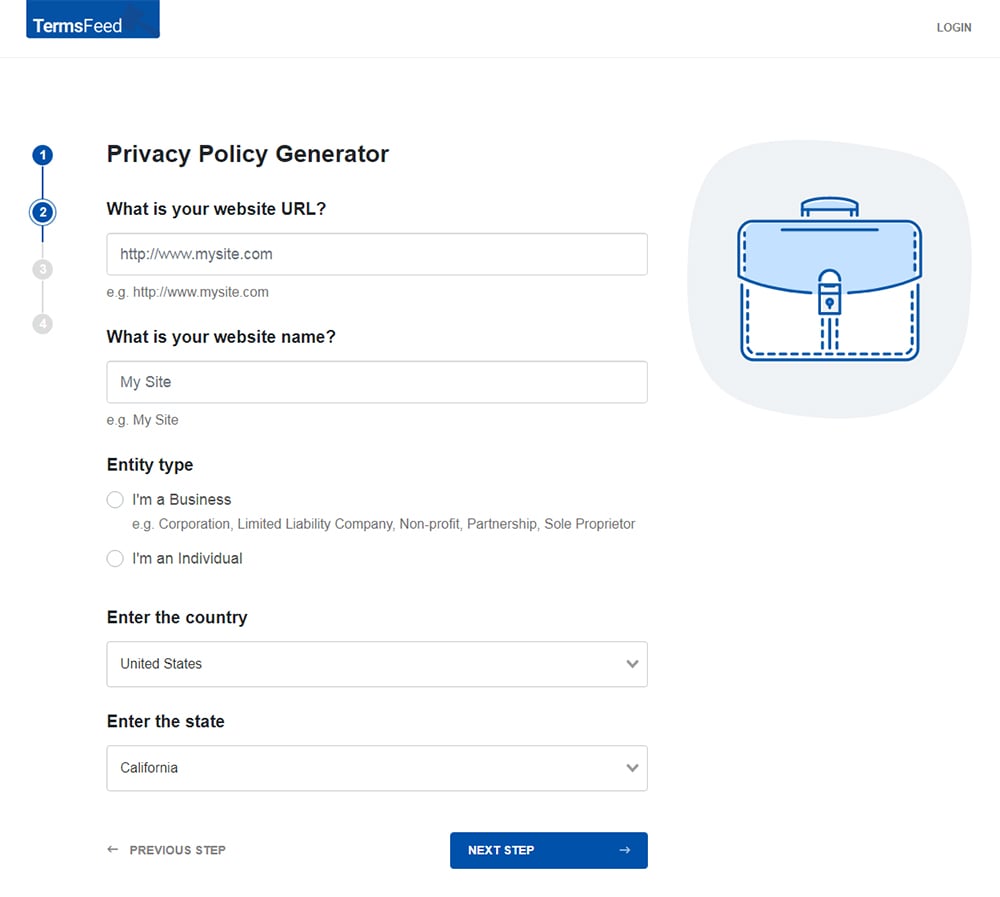
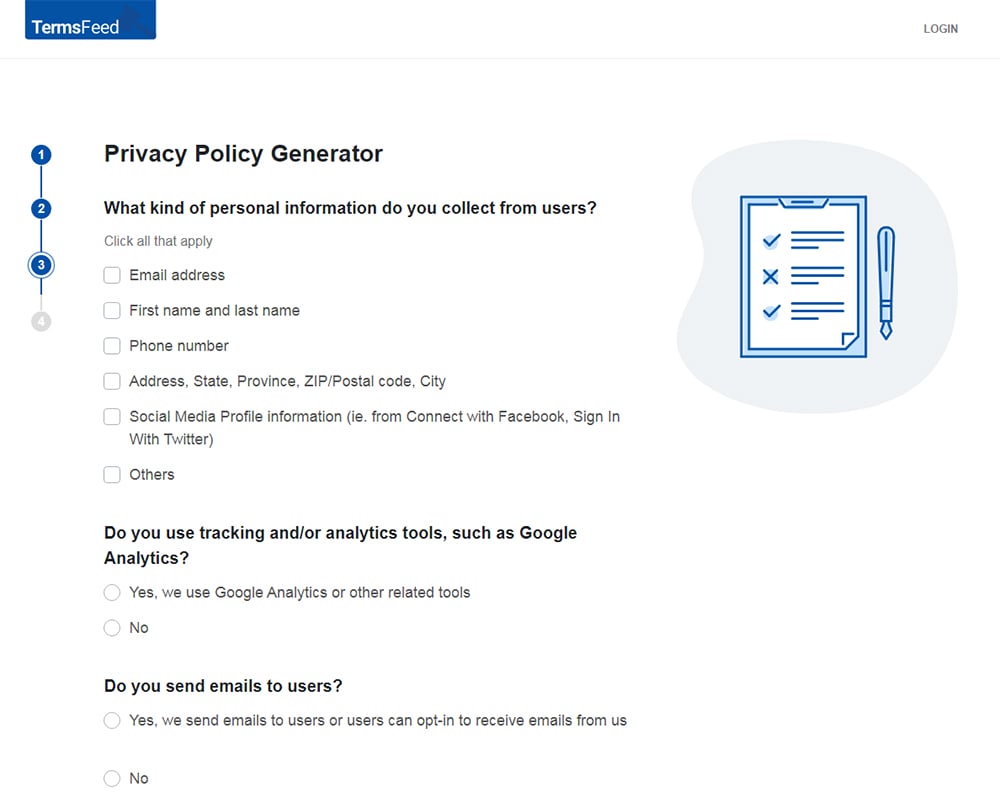
Our Privacy Policy Generator makes it easy to create a Privacy Policy for your business. Just follow these steps:
-
At Step 1, select the Website option or App option or both.
-
Answer some questions about your website or app.
-
Answer some questions about your business.
-
Enter the email address where you'd like the Privacy Policy delivered and click "Generate."
You'll be able to instantly access and download your new Privacy Policy.
- 1. Definition of "Processing" in the GDPR
- 1.1. Definition of Personal Data
- 2. Collection of Data
- 2.1. Transparency at the Point of Collection
- 2.2. Minimization of Collection
- 3. Recording
- 3.1. Recording Consent
- 3.2. Storing Records Securely
- 4. Organization and Structuring
- 4.1. Keeping Personal Data Organized
- 4.2. Conducting a Data Audit
- 5. Storage of Data
- 5.1. Storing Data Securely
- 5.2. Full Disk Encryption
- 6. Alteration
- 6.1. Altering Personal Data On Request
- 6.2. Allowing Your Users to Alter Their Own Personal Data
- 7. Disclosure by Transmission
- 7.1. Secure Transmission Within Your Organization
- 7.2. Transmitting Data to Third Parties
- 8. Erasure and Destruction
- 8.1. Right to Erasure
- 8.2. Regular Erasure of Personal Data
- 9. Summary
Definition of "Processing" in the GDPR
The definition of processing appears at Article 4(2) of the GDPR:
"'processing' means any operation or set of operations which is performed on personal data or on sets of personal data, whether or not by automated means [...]"
This definition is clearly designed to be as broad as possible. It's followed by a non-exhaustive series of examples.
"collection, recording, organisation, structuring, storage, adaptation or alteration, retrieval, consultation, use, disclosure by transmission, dissemination or otherwise making available, alignment or combination, restriction, erasure or destruction"
That covers just about everything you could conceivably do with personal data. This definition applies regardless of whether the personal data exists on paper or electronically.
We're going to take a detailed look at some of these methods of processing, consider some examples of how you might engage in them, and how they might apply in practice in relation to the GDPR's requirements.
Definition of Personal Data
Before we look at "processing," it's worth briefly defining "personal data."
Just as the definition of "processing" in EU law is extremely broad, so is the definition of "personal data."
Here's part of the definition of personal data Article 4(1) of the GDPR:
"'personal data' means any information relating to an identified or identifiable natural person ('data subject'); an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier "
So, personal data is any information that relates to an identifiable person. The GDPR is a little short on examples, but this is always interpreted very broadly.
Here are some examples provided by the European Commission:
- Name and surname
- Home address
- Email address
- Identification card number
- Location data
- IP addresses
- A Cookie ID
- The advertising identifier on a mobile phone
- Data held by a doctor or hospital including symbols that uniquely identify a person
Collection of Data

Collection is one of the types of processing that features most heavily in the GDPR.
The GDPR uses the term "collect" to refer to the practice of getting personal data directly from a data subject. It uses the term "obtain" to refer to the practice of receiving personal data from a third party.
There are many reasons that you might collect personal data from a person, for example:
- You'll need to collect a person's email address when asking them to sign up to your mailing list
- You'll need to collect a person's shipping address before you can mail them a product they've purchased.
- Your website might collect cookie data from a person's device in order to target them with personalized advertising.
Transparency at the Point of Collection
You must make every effort to present the individual with your Privacy Policy whenever you collect personal data.
Here's an example from Matomo of how to present relevant privacy information when collecting a user's email address. Note that a link to the Privacy Policy is included in the subscribe form:
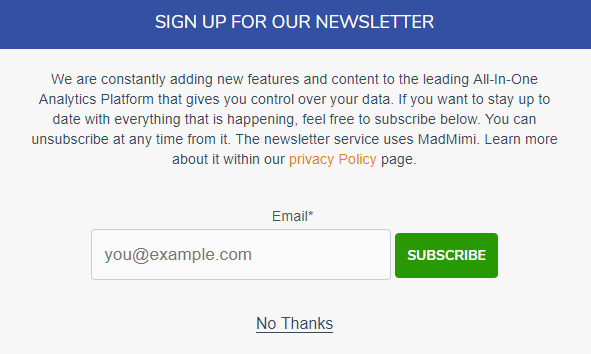
Users are informed that they can find out find out more about everything mentioned in the subscribe form by visiting the Privacy Policy.
Minimization of Collection
Don't collect personal data that you don't need. "Data minimization" is a crucially important principle under the GDPR, and can also make you less susceptible to data breaches.
- If you only need a person's email address, don't also ask for their name and date of birth.
- Be aware of personal data such as IP addresses and referral data that can be logged automatically by analytics software.
- It is always best to anonymize personal data in transit if possible.
Recording

Recording isn't formally defined in the GDPR, and can take on a few different meanings.
Under Article 30, businesses who have over 250 employees, engage in "non-occasional" data processing, or any amount of processing of special category personal data, are required to keep records of their processing activities.
However, these records are likely to be generic in nature. So this, in itself, would not constitute the processing of personal data.
Some examples of how "recording" might constitute the processing of personal data include:
- Recording that you have a person's consent for a particular type of processing
- Recording a phone call with a customer
- Keeping a record of a meeting
Recording Consent
If you've earned someone's consent to process their personal data, you must be able to demonstrate that you have done so.
The Information Commissioner's Office (ICO), the UK's Data Protection Authority, suggests recording the following information so that you can demonstrate consent:
- Who consented: Record the name or other identifier of the individual who gave consent. An "other identifier" can be an online user name or session ID.
- When they consented: Keep an online record that includes a timestamp of the consent. Paper documents and orally-given consent should also be recorded in a dated, timestamped document.
- What they were told at the time they gave consent: Keep a master copy or data capture form that has the exact statement users were presented with at the time they gave consent.
- Whether consent has been withdrawn: If consent has been withdrawn, record this and the date/timestamp of when it was withdrawn.
Storing Records Securely
When you create a record that could, either alone or when combined with other information, reveal something about an identifiable person, this record constitutes personal data. Therefore, you need to treat it with an appropriate level of security.
We'll be looking at the secure storage of personal data below. Just remember that your obligations in this area also apply to personal data that you have "created" through your recording.
Organization and Structuring

The GDPR lists the "organization" and "structuring" of personal data as two separate means of processing. Again, there is no clear explanation of these terms in the text of the GDPR.
Some examples of activities that might constitute the organization or structuring of personal data include:
- Creating a filing system to sort personal data into groups or categories
- Putting personal data into a database
- Putting a list of customer records into alphabetical order
Keeping Personal Data Organized
Organizing and structuring the personal data within your company's system is not to be discouraged. In fact, it is important for several reasons, for example:
- An individual could make a request to access, rectify or erase their personal data
- You might be required to provide personal data to the police or a court
- You might be inspected by a Data Protection Authority (DPA)
The GDPR primarily demands that you keep data secure in order that it cannot be accessed without authorization. But it also requires that you keep personal data well-organized and accessible to those who require access to it.
Conducting a Data Audit
An important step in becoming GDPR-compliant is conducting a data audit. This should involve identifying:
- The categories of personal data you process (payment details, employee records, user credentials)
- The locations where it is stored (physical filing cabinets, hard disks, cloud drives)
- Inflows (sources of personal data - web forms, email, phone calls)
- Outflows (third parties with whom you share data - mail carriers, advertisers, cloud storage companies)
Getting a handle on your records and databases is essential.
Storage of Data

Storage is another important example of data processing that features heavily in the GDPR.
Some examples of storage of personal data include:
- Keeping a list of customers' names and email addresses in a spreadsheet
- Keeping paper notes from a meeting with an employee
- Keeping emails sent to and from customers undeleted in your inbox
Storing Data Securely
The GDPR specifically mentions two methods of storing personal data securely - pseudonymization and encryption.
These two measures are often conflated, but there is a difference.
- Pseudonymization involves replacing any identifying information (personal data) in a given dataset with non-identifying information. The non-identifying information in the set may remain intelligible. But the identifying information, once pseudonymized, cannot be linked to an individual without reference to additional information.
- Encryption involves masking the entire dataset so that it will be unintelligible to anyone who does not (for example) have access to an encryption key.
Where personal data has been pseudonymized or encrypted, it must still be treated as personal data. However, there are significant advantages to using pseudonymized or encrypted data. For example, if encrypted personal data is lost during a data breach, you may not be required to inform the affected individuals that this has occurred.
Full Disk Encryption
Full disk encryption is a way to securely store personal data. This method encrypts everything contained on a disk - including any personal data.
Here are some full disk encryption facilities available for some common operating systems.
- Windows: BitLocker Drive Encryption
- Mac OS: FileVault
- Linux: LUKS
It's worth considering whether full-disk encryption might be an appropriate secure storage system within your company.
Alteration

Alteration is a an important way of fulfilling the GDPR's principle of accuracy. You might be required to "alter" personal data for a number of reasons, for example:
- You notice there is an error on a customer's record
- You need to update an employee's contact details
- A person claims that your records of their personal data are inaccurate
Wherever you have made an alteration to personal data, it is usually best to keep a record to this effect.
Altering Personal Data On Request
The GDPR allows individuals to exercise the "right to rectification." This means that if a person believes there to be an error in your record of their personal data, they have to right to request that you alter the personal data in order to rectify it.
You should inform individuals of their right to make such a request (along with information about their other rights) in your Privacy Policy.
Where receive such a request you must normally act on it within one month. You may not normally charge the individual and instead must honor the request for free.
If you're sure that the personal data is not inaccurate, you may have grounds to refuse the request.
Allowing Your Users to Alter Their Own Personal Data
If you run a website which allows people to set up an account, you should aim to offer them maximum direct control to make alterations to the personal data associated with their account.
This will save you work in the long-run, as you'll be less likely to receive requests for rectification or deletion of their personal data.
Here's Instagram's "Edit Profile" screen. Consider that all these options can qualify as "personal data" in this context.
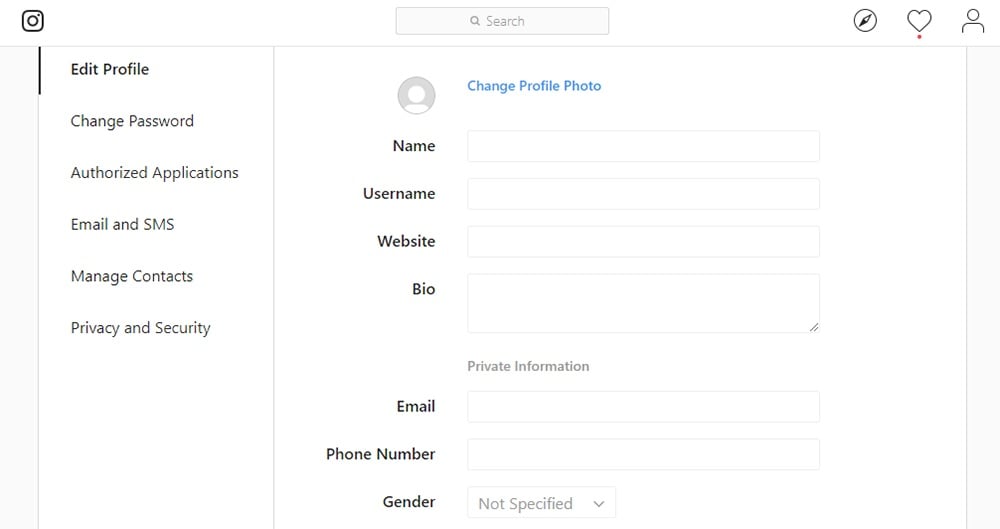
A screen like this gives your users maximum control over their data, which helps them instantly make changes they wish to make without needing to request you do so for them.
Disclosure by Transmission

The "disclosure by transmission" of personal data can include the sharing of personal data with other companies. But it can also apply to the transmission of personal data within your organization.
Here are some situations in which you might disclose personal data by transmission:
- Emailing a list of customer account details to a colleague
- Uploading personal data to a cloud drive
- Sharing customer information with an email marketing service
Secure Transmission Within Your Organization
Personal data should always be transmitted securely, so as to avoid interception. There are a number of ways to ensure security during transmission within your company, for example:
- When sending personal data files as attachments to emails, these files can first be encrypted
- Use secure network communication methods such as Transport Layer Security (TLS)
- Implement a Virtual Private Network (VPN) with encryption for remote working
Transmitting Data to Third Parties
You may need to share personal data with another organization so that they can process it on your behalf. For example, you might share personal data with companies that provide:
- Email marketing services
- Analytics
- Personalized advertising
Such companies are known as "data processors." The terms of transmitting personal data to such companies, and of their subsequent processing of that personal data, must be set out in a contract known as a Data Processing Agreement.
You may only use data processors that can demonstrate their compliance with the GDPR.
Erasure and Destruction

Erasure and destruction of personal data is a necessary part of complying with the GDPR. As we've seen, the principle of storage limitation requires that you erase personal data that you no longer need.
Here are some examples of when you might erase personal data in your possession:
- A person gave you their name and address to make a single order that has been fulfilled. If you're unlikely to need this data again, you can erase it.
- A person unsubscribes from your newsletter. You can erase their email altogether rather than retaining it elsewhere.
- You've been logging IP addresses of visitors to your site to help identify the perpetrator of a distributed denial of service attack. This threat has now been dealt with, so you can erase the data you collected for this purpose.
Right to Erasure
Under the GDPR, individuals have the right to request that you erase any personal data you hold on them. This is known as the "right to erasure," or sometimes the "right to be forgotten."
This is not an absolute right, and it may be appropriate to refuse under certain conditions.
When someone requests that you erase their personal data, it's best to explain the implications of this. Here's an example from Facebook:

Users are told that information like photos, videos and posts will be irretrievable and permanently gone, but that some information, like sent messages, will be stored in the recipient's inbox.
Regular Erasure of Personal Data
One of the GDPR's principles of data processing is storage limitation. You must not store personal data for longer than you need it in connection with a specified purpose.
This means that you should schedule regular points at which different categories of personal data are erased.
It is important to be able to justify how long you keep each type of personal data you store. This might involve drawing up a Retention Schedule, which clearly sets out your storage periods.
Here's an excerpt from the ICO's Retention Schedule:
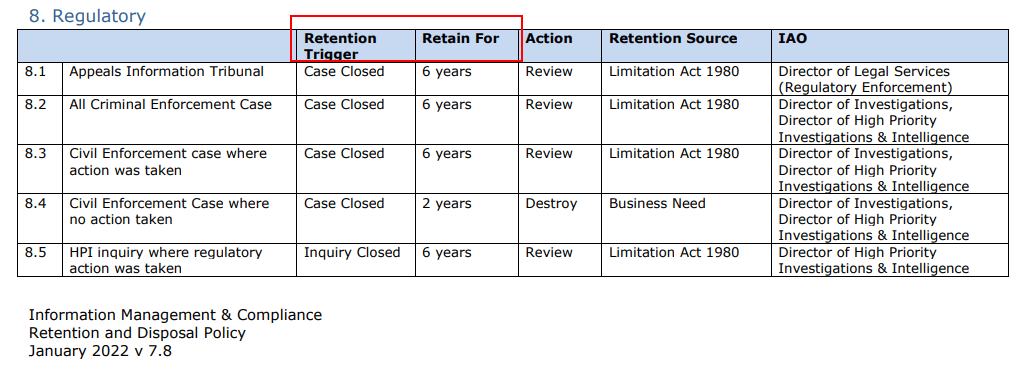
Note how it includes how long something will be retained for, what action will occur after that time period, and who owns the information asset at the moment.
Summary
We've seen that "processing" really can mean doing anything with personal data - even if that means just letting it sit in filing cabinets or servers.
Here are some important things to consider in connection with your company's data processing practices:
- When collecting personal data, ensure that you:
- Present an individual with privacy information such as your Privacy Policy
- Only collect the personal data necessary for fulfilling a specified purpose
- When making records of personal data:
- Make them as specific as required, particularly in relation to recording consent
- Remember that where a record constitutes personal data it must be stored securely
- When organizing or structuring personal data:
- Keep personal data accessible (to those with authorization to access it)
- Conduct regular data audits within your company
- When storing personal data:
- Employ technical measures such as pseudonymization and encryption
- Consider full disk encryption methods where appropriate
- When making alterations to personal data:
- Ensure you have an efficient system for receiving and responding to rectification requests
- Hand individuals as much direct control over their personal data as is appropriate
- When disclosing personal data by transmission:
- Employ technical measure within your own company's networks to ensure secure transmission of personal data
- Whenever you're considering transmitting personal data to third parties, ensure that you have the appropriate written agreements in place, and that you have checked that they are GDPR-compliant
- When erasing or destroying personal data:
- Ensure you have an efficient system for receiving and responding to erasure requests
- Create a Retention Schedule which sets predetermined points at which different categories of personal data will be erased

Comprehensive compliance starts with a Privacy Policy.
Comply with the law with our agreements, policies, and consent banners. Everything is included.